In 2025, remote workforces aren’t the exception—they’re the expectation. Whether supporting hybrid schedules, distributed teams, or fully remote operations, organizations now rely on secure remote access as a baseline, not a luxury. With that shift, the tools used to connect people to their work environments are under more scrutiny than ever.
For years, VPNs and Citrix were the dominant players in the remote access space. VPNs offered a direct tunnel into corporate networks, while Citrix provided virtual desktops and application access through centralized servers.
Both earned their place in enterprise IT stacks. But as business needs evolved—and security threats grew—so did the cracks in these legacy systems.
Now, many businesses are asking a sharper question: Citrix vs VPN—which still makes sense? Or is it time to rethink the model entirely?
In this post, you’ll explore the core differences between these solutions, what they offer today, and how modern alternatives like Apporto are reshaping the conversation around remote work.
What Is a VPN and How Does It Work for Remote Access?
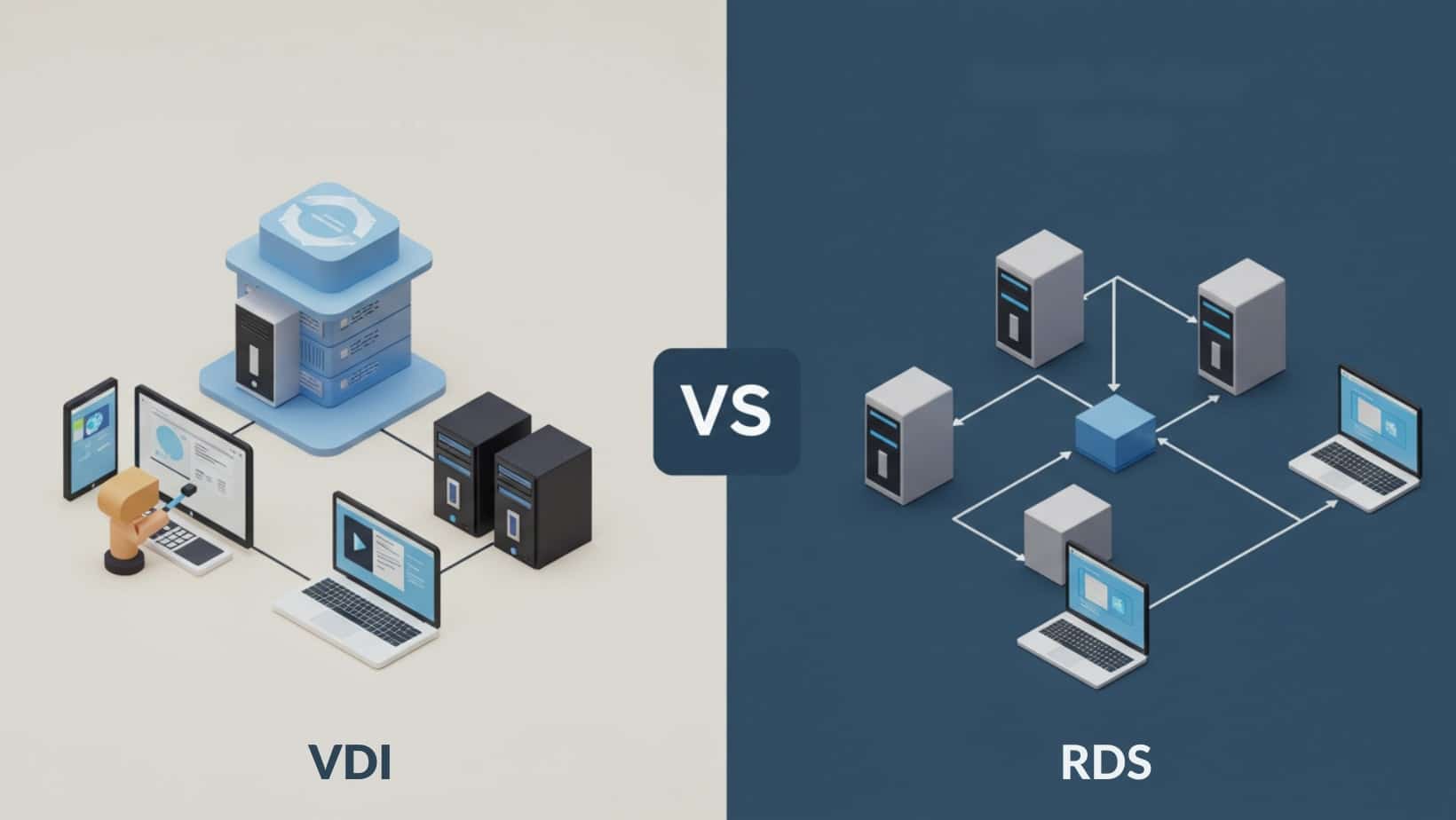
A Virtual Private Network (VPN) creates a secure, encrypted tunnel between a user and their organization’s network. When remote users connect to a VPN server using a VPN client, they gain full access to internal systems, applications, and resources—just as if they were sitting in the office.
The basic idea is straightforward: the VPN connection masks the user’s location and routes all traffic through the company’s private network, even if they’re working from a public network like a café or airport Wi-Fi. This allows for secure communications and helps keep sensitive data away from prying eyes.
There’s a reason VPNs are still widely used. They’re often simpler to deploy, relatively low-cost, and compatible with most devices. Many businesses rely on traditional VPN tools to enable basic remote access, especially for occasional users or small teams.
However, this method has real limitations. VPNs grant broad access to the network, which increases the risk of data exposure if a device is compromised. They also offer minimal control over user behavior and endpoint security. Once inside the network, users can access far more than they might need—and that makes access control a growing concern for IT teams.
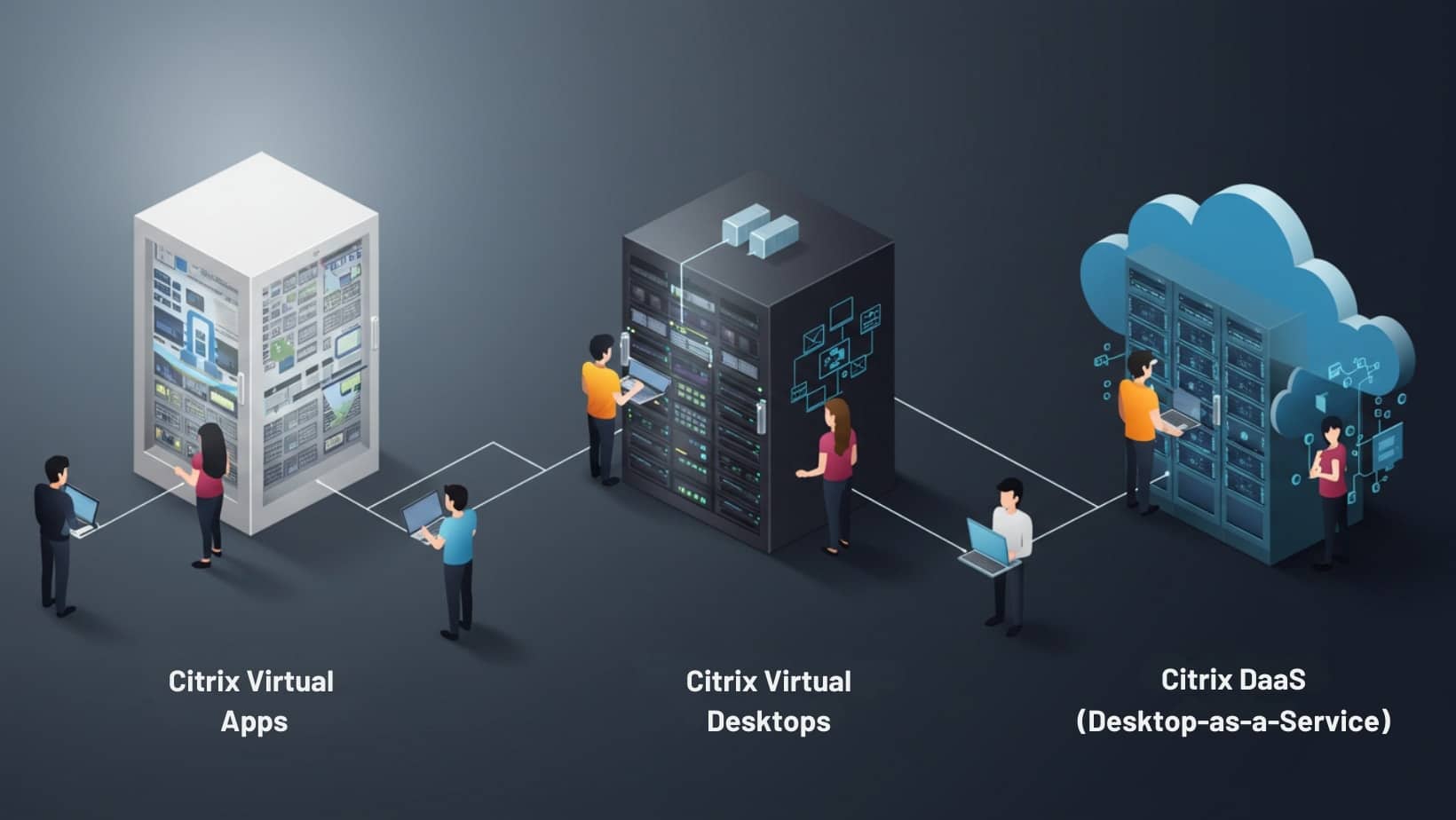
What Is Citrix and How Does It Differ from a VPN?

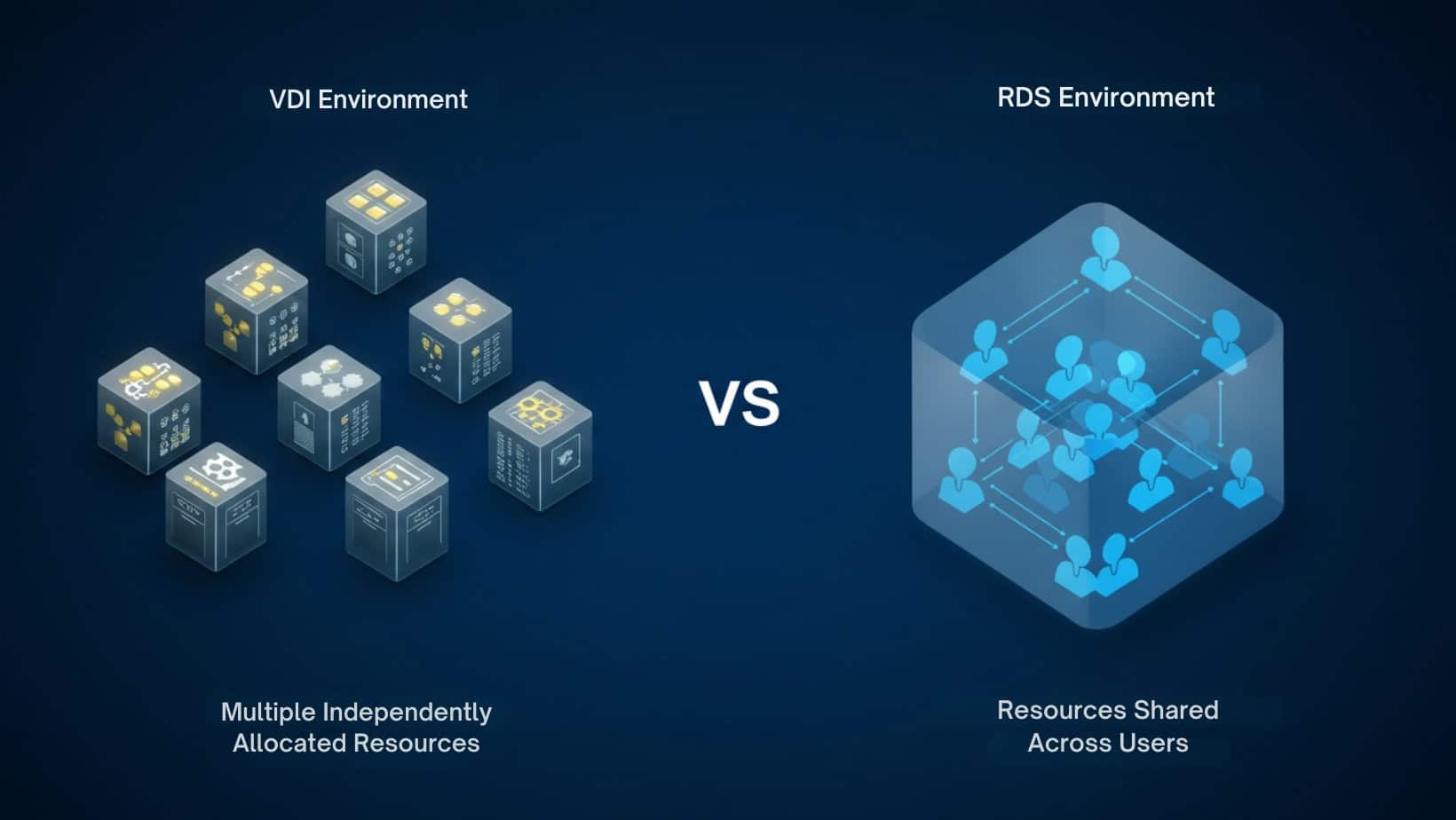
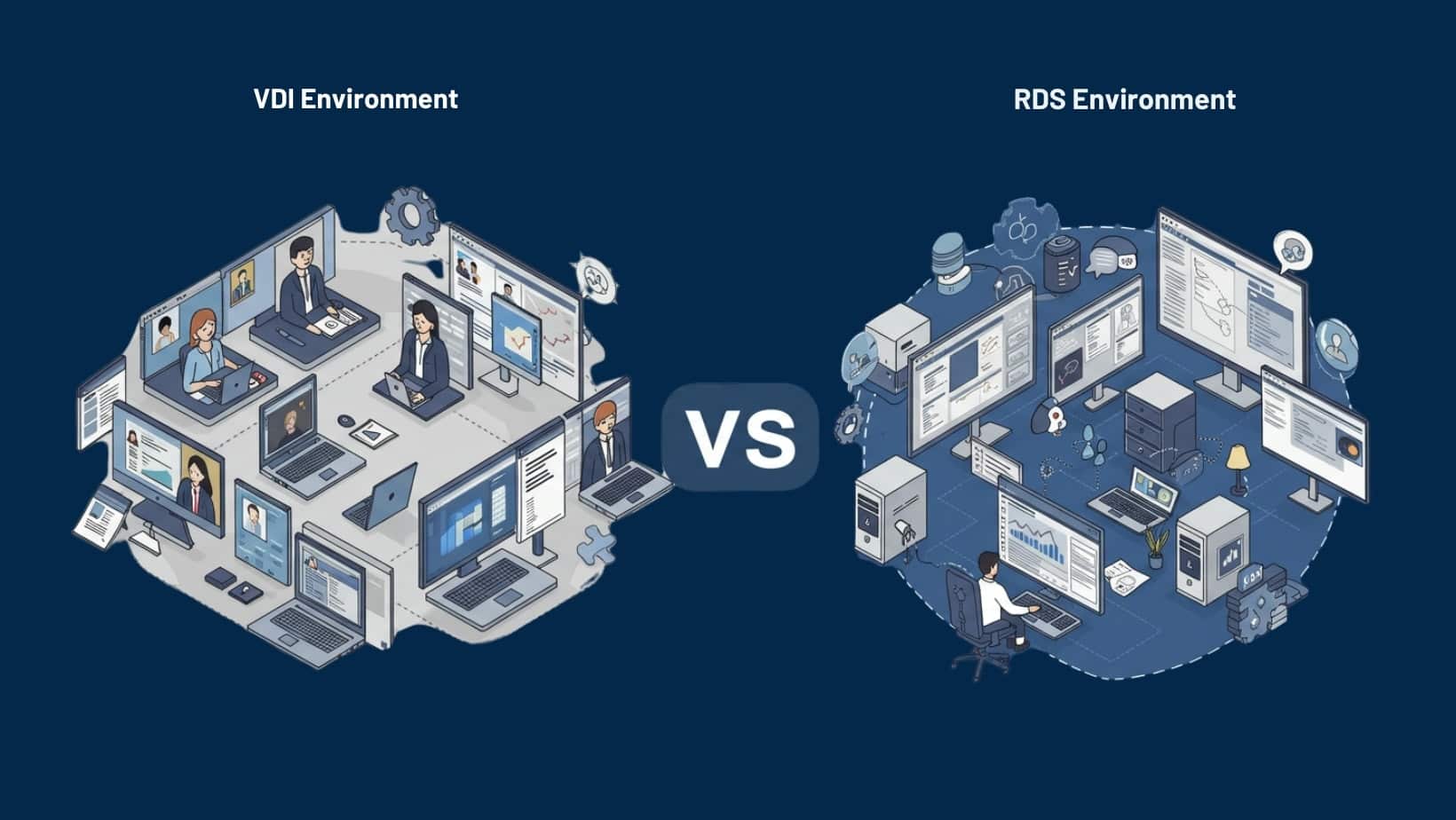
Citrix is a virtualization solution that delivers remote access through virtual desktop infrastructure (VDI). Instead of tunneling into the network like a VPN, Citrix provides a hosted desktop environment or individual apps from a centralized Citrix server. Users interact with this virtualized interface from any device, but the data and processing remain on the server.
This model gives IT teams greater control over remote devices, because sensitive applications never actually leave the data center. It’s all streamed in real-time. Citrix is particularly known for its use in regulated industries, where data security and central management are key.
The difference between Citrix and VPN is structural. A VPN gives users access to everything on the internal network—it’s a wide open door. Citrix, on the other hand, builds a controlled experience, limiting exposure and keeping sensitive data off endpoint machines.
That added security comes with complexity. Citrix licenses, server infrastructure, and setup can be resource-intensive, which may not be ideal for lean IT teams. Still, for many businesses, especially those in cloud computing or with strict compliance requirements, Citrix offers an appealing alternative to broad VPN access—just with more overhead.
How Do Citrix and VPN Compare on Key Features?
When comparing Citrix vs VPN, it’s not just about how users connect—it’s about what happens once they do. Below are four core categories where the differences really show up.
1. Which Is Better for Data Security and Compliance?
If data security is your top concern, Citrix generally has the edge. A VPN encrypts the data transmission between a device and the network, but once the tunnel is open, all that sensitive data is exposed on the user’s local machine. If that machine is compromised, so is your data.
Citrix, in contrast, keeps everything on the server. Users interact with a virtualized session, but no data is actually transferred to the endpoint. This creates a secure network boundary and reduces the risk of unauthorized data transfer. For businesses in healthcare, finance, or education, that separation can make meeting regulatory requirements easier and more reliable.
2. What About User Experience and Device Compatibility?
From the user’s perspective, VPNs are typically faster to set up but can be clunky in practice—especially when used from a remote location with poor bandwidth. Performance is dependent on both the user’s device and the quality of the network connection.
Citrix is more consistent across platforms, since it delivers a controlled experience regardless of hardware or operating system. That said, if the existing systems aren’t optimized for Citrix, the interface can feel sluggish. In general, Citrix wins on functionality, but VPNs still offer a lighter footprint for basic tasks.
3. Which Solution Offers Better Control for IT Teams?
If your IT team values centralized management, Citrix offers more control. Administrators can define session policies, push updates, and restrict user actions—without touching the physical device.
VPNs give remote users open access to network resources, which is harder to govern. While this can be efficient in smaller setups, it increases risk as the number of users grows. For large or sensitive environments, Citrix significantly reduces the burden on IT by keeping everything in one place.
4. How Do Costs and Infrastructure Compare?
VPN solutions usually come with lower upfront costs. You’ll need a VPN server, client software, and basic support—making it appealing for budget-conscious teams.
Citrix, on the other hand, requires investment in licenses, infrastructure, and skilled IT support. However, it may deliver a better return as your organization grows, especially if centralized access, security, and compliance are priorities.
Ultimately, VPN is more affordable short-term. Citrix—and modern platforms like Apporto—offer an added benefit in scalability and risk reduction that can pay off in the long run.
When Does a Traditional VPN Still Make Sense?

A VPN solution remains a valid choice in certain cases. For small organizations with limited budgets and basic needs, VPNs offer a simple and low-cost way to connect remote users to internal resources. If your team just needs to access email or internal file servers from a remote location, a VPN service can work without much overhead.
VPN offers quick deployment and flexibility, especially when no centralized infrastructure is in place. However, the tradeoff is control. As your team scales or your data becomes more sensitive, VPNs struggle to address growing security and compliance needs. What works well for five users may not work at all for fifty.
When Should You Use Citrix or a Virtualization Platform Instead?
If you’re managing distributed teams, sensitive workloads, or regulated data, Citrix—or a more modern alternative like Apporto—is usually the better fit. These virtualization solutions offer virtual desktops delivered from a centralized, secure environment, ensuring better visibility and control.
Unlike VPNs, Citrix makes it easier to manage apps, apply policies, and restrict data movement across remote devices. With strong cloud integration and scalable infrastructure, platforms built on virtual desktop infrastructure support both growth and secure remote access.
If your existing systems are straining under the weight of remote work, it may be time to move beyond VPN.
Can You Use Both Citrix and VPN Together?

Some organizations use both Citrix and VPN as part of layered remote access strategies. A VPN may provide broad network services access, while Citrix is used to deliver specific applications or remote desktops. In certain legacy environments, this dual setup can help bridge gaps between new and old systems.
But pairing them comes at a cost. Running both increases licensing, adds complexity, and can confuse VPN users who aren’t sure which path to take. You also lose centralized control—especially when remote devices switch between platforms.
Just because you can combine Citrix and VPN doesn’t mean you should. In most cases, one well-executed solution is more efficient than two overlapping ones.
Why Apporto Is a Smarter Alternative to Both Citrix and VPN
Apporto is a browser-based platform built on a Zero Trust model—no VPN clients, no Citrix licenses, and no need to expose your internal infrastructure to outside devices.
It provides a secure connection to virtual desktops and apps without installing anything locally. That means remote devices stay isolated, and data stays protected—by default.
Designed for teams who prioritize both speed and security, Apporto eliminates the complexity of legacy platforms and simplifies how IT delivers access in a cloud computing world.
No tunnels. No clients. Just seamless access that works anywhere. Try Apporto now
Final Thoughts: Which Solution Fits Your Business Best?
Choosing between Citrix and VPN isn’t just a technical decision—it’s a strategic one. You’re weighing security, scalability, cost, and ease of access for your users. While VPNs still serve basic needs, they rarely scale well. Citrix offers more control but often demands more from your infrastructure and IT teams.
Modern environments need more than outdated software layers. They need solutions built for how people actually work—secure, simple, and flexible.
If you’re rethinking how your team connects to your network, consider whether you’re holding onto what’s familiar… or moving toward what actually works.
Frequently Asked Questions (FAQs)
1.Is Citrix more secure than a VPN?
Yes. Citrix keeps data centralized and off endpoint devices, while VPNs transmit it across potentially untrusted networks.
2.Can Citrix and VPN be used together?
They can, but using both can increase cost, complexity, and user confusion.
3.Which is easier to deploy—Citrix or VPN?
VPN is easier to set up initially, but Citrix offers better long-term control and user management.
4.Is a VPN still good for remote access?
Yes—for small teams or simple use cases. But it offers limited secure remote access at scale.
5.What’s the best alternative to Citrix and VPN?
Apporto offers a browser-based, Zero Trust platform that simplifies remote access while strengthening security and lowering overhead.