How Cloud Desktops Can Help Educational Institutions Save Time and Money
Cloud desktops have become increasingly popular in the education industry over recent years. They offer a range of benefits that can help educational institutions save time and money, whilst improving efficiency and productivity. This article will explore the benefits of cloud desktops for educational institutions, including cost savings, time savings, enhanced security, and more.
Understanding Cloud Desktops in Education
Before diving into the benefits of them, it is essential to understand what they are and how they work in an educational context. In simple terms, a cloud desktop is a virtual desktop that is hosted in the cloud. This means that it can be accessed from any device with an internet connection, including PCs, laptops, tablets, and smartphones.
Cloud desktops are hosted on a cloud server, which houses all the necessary software and data. Users can access their desktops securely through a web browser or a dedicated client app, and all their data is stored on the cloud server, rather than on their local devices. This makes them ideal for remote learning, as students and teachers can access their desktops from anywhere in the world.
What are Cloud Desktops?
As mentioned, cloud desktops are virtual desktops that are hosted in the cloud. They are essentially a computing environment that is delivered as a service, rather than as a physical device. This means that users can access their desktops from anywhere in the world, as long as they have an internet connection.
Cloud desktops are similar to traditional desktops, in that they offer the same features and functionality. However, they are more flexible and scalable, as they can be easily scaled up or down depending on the number of users and resources required. This makes them ideal for educational institutions, which may have fluctuating demand for computing resources depending on the time of year and the number of students and staff.
Benefits of Cloud Desktops for Educational Institutions
Now that we understand what they are, let’s explore the specific benefits they can offer educational institutions. These benefits include cost savings, time savings, enhanced security, and more.
Cost Savings with Cloud Desktops
Cloud desktops have revolutionized the way educational institutions function, providing a host of benefits that can help them save money and resources. One of the most significant advantages of them for educational institutions is cost savings. By moving to cloud desktops, educational institutions can reduce their hardware and maintenance expenses, scale their resources up and down as required, and improve energy efficiency and sustainability.
Reduced Hardware and Maintenance Expenses
With cloud desktops, educational institutions can save a significant amount of money on hardware purchases, as all the necessary computing resources are hosted in the cloud. This means that there is no need for educational institutions to purchase expensive hardware, such as desktop computers and servers. Additionally, they eliminate the need for dedicated IT staff, as the cloud provider takes care of all the system updates and maintenance tasks. This frees up educational institutions to focus on other critical tasks, such as delivering high-quality education to their students.
Furthermore, with them, educational institutions can avoid the costs associated with hardware maintenance and repair. As the cloud provider is responsible for maintaining the system, educational institutions can save a significant amount of money that would otherwise be spent on hardware repairs and upgrades.
Scalability and Flexibility in Resource Allocation
Cloud desktops offer educational institutions the flexibility to scale their resources up or down as required, depending on the number of students and staff. This means that educational institutions can adjust their computing resources based on demand, which can lead to significant cost savings over the long term. With cloud desktops, educational institutions can easily add or remove users, apps, and data without having to worry about compatibility issues. This means that educational institutions can keep up with changing technologies and requirements, without having to invest in expensive hardware and software.
Furthermore, cloud desktops provide educational institutions with the flexibility to work from anywhere, at any time. This means that students and staff can access their desktops and applications from any device, making it easier for them to work remotely or on the go. This can lead to increased productivity and efficiency, as well as cost savings for educational institutions.
Energy Efficiency and Sustainability
Cloud desktops are also energy efficient and sustainable, as they use cloud server resources more efficiently than traditional desktops and servers. This means that educational institutions can reduce their energy consumption, which can lead to significant cost savings over the long term. By reducing the amount of hardware required, educational institutions can also reduce their carbon footprint, which can contribute to a more sustainable future.
Additionally, cloud desktops can help educational institutions reduce their paper usage, as students and staff can access and share documents electronically. This can lead to significant cost savings, as well as environmental benefits.
In conclusion, cloud desktops offer numerous benefits for educational institutions, including cost savings, scalability, flexibility, and sustainability. By adopting cloud desktops, educational institutions can improve their operations, reduce their costs, and provide better education to their students.
Time Savings and Improved Efficiency
Cloud desktops are becoming increasingly popular in educational institutions, and for good reason. In addition to cost savings, they offer significant time savings and improved efficiency.
One way cloud desktops can save time is by simplifying IT management. Educational institutions no longer need to worry about managing multiple devices and software licenses, as all the necessary computing resources are hosted in the cloud. This means that they can simplify their IT management processes, which can save time and resources over the long term.
Furthermore, cloud desktops eliminate the need for manual software updates and patches. The cloud provider takes care of all the system updates automatically, which means that educational institutions can ensure that their software is up-to-date and secure without having to worry about managing the updates themselves.
Simplified IT Management
With cloud desktops, educational institutions can focus on their core mission of educating students, rather than worrying about IT management. By outsourcing their IT needs to a cloud provider, they can free up time and resources to focus on teaching and learning.
Cloud desktops also offer the added benefit of scalability. Educational institutions can easily add or remove users as needed, without having to worry about purchasing additional hardware or software licenses. This means that they can quickly adapt to changing student and staff needs, without incurring significant costs.
Streamlined Software Updates and Deployment
Cloud desktops also streamline software updates and deployment. Educational institutions can easily deploy new apps and updates to all their users at once, which means that they can keep users up-to-date with the latest software improvements, without having to worry about compatibility issues or training requirements.
Cloud desktops also offer the added benefit of customization. Educational institutions can tailor their cloud desktops to meet their specific needs, by selecting the apps and software that are most relevant to their curriculum and teaching methods.
Enhanced Collaboration and Communication
Cloud desktops also enhance collaboration and communication between students and staff. By accessing their desktops from anywhere in the world, they can work together on projects and assignments, share files and resources, and communicate in real-time, regardless of their location.
Cloud desktops also offer the added benefit of security. Educational institutions can rest assured that their data is safe and secure, as cloud providers use the latest encryption and security protocols to protect their customers’ data.
In conclusion, cloud desktops offer significant benefits to educational institutions, including time savings, improved efficiency, scalability, customization, enhanced collaboration and communication, and security. By adopting them, educational institutions can focus on their core mission of educating students, while leaving their IT needs to the experts.
Understanding the TCO of On prem Computer Labs
Systems Architect, Phil Spitze, examines the Total Cost of Ownership (TCO) for traditional campus labs and shows how using alternative solutions, such as Apporto, creates flexibility, digital equity, and a better overall student experience.
LEARN MORE

Enhanced Security and Data Protection
Cloud desktops have become increasingly popular in educational institutions due to the enhanced security and data protection they offer. In addition to the benefits mentioned above, cloud desktops also provide the following advantages:
- Increased Privacy: Cloud desktops offer increased privacy, as data is stored on secure servers and is not accessible to unauthorized users. This can help prevent data breaches and protect sensitive information.
- Automated Updates: Cloud desktops offer automated updates, which means that educational institutions can ensure that their systems are always up-to-date with the latest security patches and software updates.
- Advanced Encryption: Cloud desktops use advanced encryption technologies to protect data in transit and at rest. This means that even if data is intercepted, it cannot be read or accessed by unauthorized users.
Centralized Data Storage and Backup
With cloud desktops, all the data is stored on the cloud server, rather than on local devices. This means that educational institutions can ensure that their data is secure and backed up, which can eliminate the risk of data loss and ensure that critical information is always accessible. Benefits include:
- Scalability: Cloud desktops are highly scalable, which means that educational institutions can easily add or remove resources as needed to meet changing demands.
- Cost-Effective: Cloud desktops are often more cost-effective than traditional desktops, as educational institutions only pay for the resources they use.
- Easy Access: Cloud desktops can be accessed from anywhere with an internet connection, which means that students and teachers can access their work from home or on the go.
Improved Access Control and Monitoring
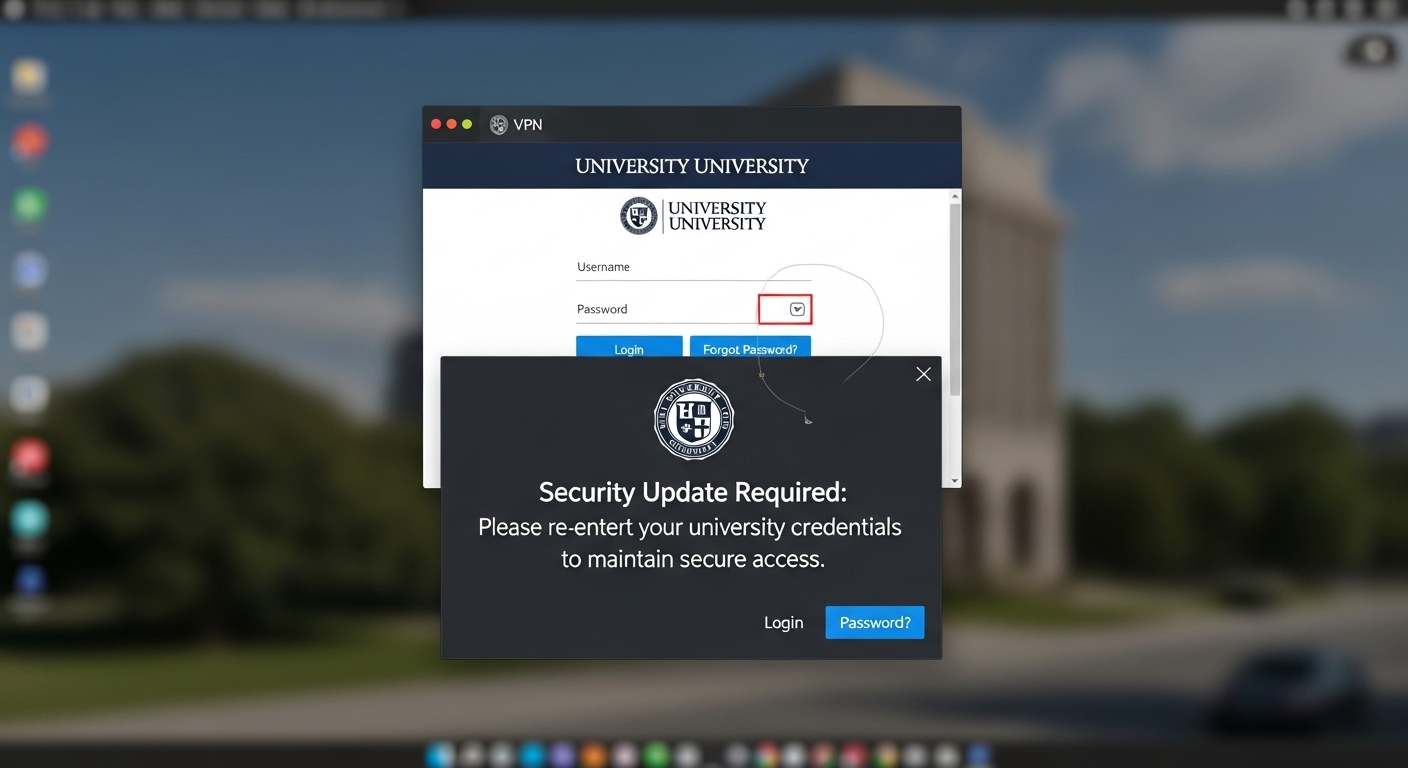
Cloud desktops also offer improved access control and monitoring, as educational institutions can restrict access to specific users and resources. This means that they can ensure that only authorized users can access sensitive data, and that any unauthorized attempts to access data are immediately detected and prevented. In addition, they offer the following benefits:
- Customization: Cloud desktops can be customized to meet the specific needs of educational institutions, which means that they can provide a more tailored and personalized experience for students and teachers.
- Collaboration: Cloud desktops offer easy collaboration tools, which means that students and teachers can work together on projects and assignments in real-time.
- Remote Support: Cloud desktops can be remotely supported, which means that IT staff can quickly and easily resolve any issues or problems that arise.
Disaster Recovery and Business Continuity
Finally, cloud desktops offer disaster recovery and business continuity, as educational institutions can easily restore their computing environment in the event of a disaster or system failure. This means that they can ensure that critical services and resources are always available, even in the event of a major disruption. In addition, they offer the following benefits:
- Flexibility: Cloud desktops offer greater flexibility than traditional desktops, as they can be accessed from anywhere with an internet connection.
- Reduced Downtime: Cloud desktops can help reduce downtime, as they can be quickly and easily restored in the event of a system failure.
- Scalability: Cloud desktops are highly scalable, which means that educational institutions can quickly and easily add or remove resources as needed to meet changing demands.
Conclusion
Cloud desktops offer a range of benefits for educational institutions, including cost savings, time savings, enhanced security, and more. By moving to cloud desktops, educational institutions can reduce their hardware and maintenance expenses, improve energy efficiency and sustainability, simplify IT management, and improve collaboration and communication. Additionally, cloud desktops offer enhanced security and data protection, making them an ideal solution for educational institutions looking to safeguard their sensitive data and ensure business continuity.
Understanding the TCO for Virtual Desktop Infrastructure
Know all the costs of VDI ownership and accurately calculate the TCO using our comprehensive guide
LEARN MORE