Traditional network security was built around a perimeter. Once someone was inside, they were trusted. That model no longer works.
Today’s networks are borderless, spanning remote workers, cloud apps, mobile devices, and third parties. The attack surface has widened, and with it, the risk of insider threats and breaches.
Zero Trust Security replaces assumptions with verification. It treats every user, device, and request as untrusted until proven otherwise.
In this post, you’ll explore why Zero Trust is becoming the backbone of modern security strategies.
What Is Zero Trust Security and How Is It Different from Traditional Security Models?
Zero Trust Security is a modern cybersecurity model built around one simple principle: never trust, always verify. That means no user or device, whether inside or outside the network, is automatically trusted. Every request to access data, apps, or systems must be verified first, every time.
In contrast, traditional security models are based on a defined network perimeter.
The assumption is that threats come from outside, and once a user gains access to the internal network (often via VPN or physical location), they are trusted. This implicit trust leaves the organization vulnerable to insider threats, lateral movement by attackers, and unmonitored access to sensitive data.
The Zero Trust model eliminates that risk by rejecting the perimeter mindset entirely. It doesn’t matter where the request originates, access is granted based on strict verification of identity, device health, context, and policy. This is called least privilege access, and it ensures users only get access to what they absolutely need.
Main differences between traditional and Zero Trust security strategies:
| Feature | Traditional Security Models | Zero Trust Security Model |
|---|---|---|
| Trust Model | Implicit trust inside the network | No implicit trust; verify every request |
| Network Perimeter | Strong focus on a secure boundary | Assumes perimeter is already compromised |
| Access Control | Broad, often static | Granular and dynamic |
| Monitoring | Perimeter-focused | Continuous and identity-driven |
Adopting a Zero Trust strategy means shifting from a “trusted until proven risky” approach to a “never trusted, always validated” model. This is especially critical for today’s organizations, where users and devices connect from anywhere and network traffic flows across cloud, on-prem, and hybrid environments.
Ultimately, Zero Trust is not just a new technology, it’s a complete rethink of how trust should work in a modern IT environment.
How Does Zero Trust Architecture Actually Work?
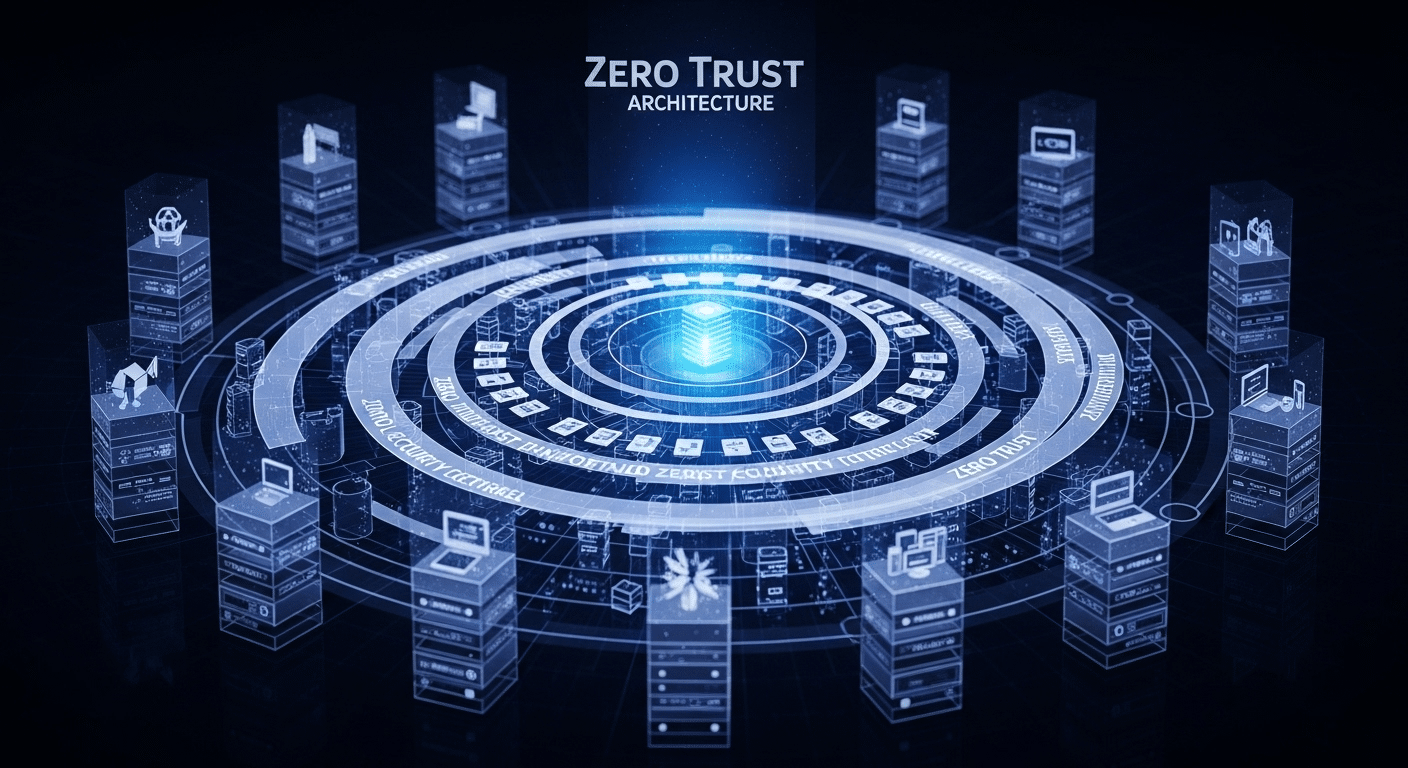
While the Zero Trust model is a philosophy, the Zero Trust architecture is how it’s implemented. It brings structure to that philosophy, ensuring that access control, visibility, and verification happen consistently across the organization.
At the heart of this architecture is ZTNA, Zero Trust Network Access. Unlike traditional VPNs that grant full access once connected, ZTNA allows users to access only specific apps or services, based on their identity, device status, and security posture. It acts as a smart gatekeeper, one that doesn’t assume your identity just because you’re inside.
Core components of a Zero Trust architecture include:
- Identity Verification
Every user must authenticate using multi-factor authentication (MFA), Single Sign-On (SSO), and contextual signals. - Device Validation
Devices are assessed for compliance, health, and security before access is granted. - Network Traffic Monitoring
Every data packet is inspected. East-west (internal) traffic is monitored just as closely as north-south (external) traffic. - Least Privilege Access
Users receive access to only what they need, nothing more. - Continuous Monitoring
Trust is never permanent. Sessions are reassessed and reevaluated in real time.
Leading Zero Trust platforms often integrate with existing tools to enforce these rules automatically. Many follow guidance from agencies like the National Institute of Standards and Technology (NIST) and the Cybersecurity and Infrastructure Security Agency (CISA), which have laid out frameworks for Zero Trust in federal and enterprise environments.
The goal is to continuously verify users and devices, protect network infrastructure, and reduce the risk posed by implicit trust, no matter where the access request comes from.
What Are the Core Principles of Zero Trust?
The Zero Trust model is guided by a set of principles that define how access and security should function in a modern IT environment. These aren’t just technical rules, they’re philosophical shifts in how organizations think about trust, access, and risk.
Here are the core principles of Zero Trust, as outlined by the National Institute of Standards and Technology (NIST) and widely adopted across industries:
1. Least Privilege Access
This principle ensures that users, and even devices, are granted the minimum level of access required to perform their role. Nothing more. This limits the potential damage from compromised accounts or insider threats.
2. Continuous Verification
Authentication isn’t a one-time event. With Zero Trust, access is continuously verified throughout a session. That includes checking user behavior, device posture, location, and network context in real time.
3. Granular Access Control
Access decisions are dynamic. Access control policies consider who is requesting access, what they’re trying to reach, where they’re coming from, and how secure their device is.
4. Micro-segmentation
Rather than having one large, flat network, micro-segmentation breaks the infrastructure into smaller zones. Each one requires its own authentication and policies. If one zone is breached, the threat can’t easily spread.
5. Assume Breach
Zero Trust operates on the belief that breaches are inevitable. By assuming breach, the system is designed to minimize impact rather than reacting after damage is done.
These Zero Trust concepts build a framework that aligns with real-world threats. By following the principle of least privilege and layering in smart access decisions, Zero Trust transforms your security posture into something proactive, adaptive, and deeply resilient.
Why Is Zero Trust Adoption Growing So Fast?
The rapid rise of Zero Trust adoption is not a trend, it’s a response to real pressure. Organizations today are navigating a security landscape that’s more complex, distributed, and unpredictable than ever.
Several forces are driving the shift:
- Remote Workers
With employees accessing systems from homes, coffee shops, and mobile devices, the network perimeter is gone. Zero Trust provides secure remote access without relying on outdated VPNs. - Cloud Security
The move to cloud platforms has shattered the traditional security model. With applications and data stored across multiple environments, Zero Trust architecture becomes essential to control access at every layer. - Supply Chain Attacks
High-profile breaches (like SolarWinds) revealed how attackers exploit trusted third parties. Zero Trust assumes that no external connection is inherently safe, reducing risk from supply chain attacks. - Insider Threats and Expanded Attack Surfaces
Even legitimate users can pose a risk. Zero Trust’s continuous monitoring and least privilege access help mitigate insider threats by reducing what users can see or do unnecessarily.
Government mandates are accelerating the movement. The federal zero trust strategy, rolled out by the U.S. federal agencies, is requiring organizations to adopt Zero Trust frameworks as a matter of national cybersecurity.
In a world of rising attacks and shrinking boundaries, Zero Trust aligns with how modern IT environments actually work. It’s less about locking everything down, and more about unlocking secure, smart, and flexible access for those who truly need it.
What Is the Role of Access Management in a Zero Trust Environment?
In a Zero Trust environment, access management is no longer just a gate at the perimeter, it’s a continuous process that happens at every layer of the network. It’s not about where the request comes from, but who is requesting access, what they’re requesting, and under what conditions.
Traditional systems might grant access based on network location or login credentials. But Zero Trust demands real-time evaluation of each access request.
The system checks the user identity, evaluates the device posture, reviews behavioral patterns, and only then decides whether to grant access to a resource.
Here’s how it works:
- Requesting Access: Users initiate access to a file, application, or system.
- Verification: Their identity, device, location, and risk level are evaluated.
- Control Access: Policies determine what level of access is appropriate, if any.
- Trust Environment: Access is granted only under strict, pre-defined rules, and never permanently.
This model aligns with the principle of least privilege, meaning users can access only what they need, nothing more. Permissions are dynamic and can change in real-time based on new inputs (such as location changes or suspicious behavior).
Unlike traditional setups that rely on a one-time login, Zero Trust environments continuously verify identity and context. This ensures that if a session becomes risky, access can be revoked instantly, without compromising other systems.
Ultimately, access management in Zero Trust is about precise control, reducing unnecessary exposure, and creating a trust architecture where access is earned—not assumed.
How Do Security Teams Implement Zero Trust in Practice?

Transitioning to a Zero Trust model isn’t about ripping and replacing your existing infrastructure. It’s about reshaping your security posture around smarter, more adaptive security measures. For security teams, that means building trust from the ground up—one layer at a time.
Here’s how implementation typically unfolds:
1. Map the Network and Resources
Understand what assets need protection. Identify users and devices, sensitive data, essential applications, and critical infrastructure. This forms the foundation for applying security controls.
2. Establish Strong Identity and Access Management (IAM)
Enforce multi-factor authentication (MFA), centralize identity via SSO, and implement role-based access control. This ensures each access request is tied to a verifiable user identity.
3. Apply the Principle of Least Privilege
Use policy engines to grant access only to necessary resources. Remove unnecessary permissions and ensure access is time-bound or context-aware.
4. Enforce Continuous Monitoring and Verification
Adopt tools that enable continuous verification of users, devices, and network traffic. This includes endpoint detection, behavioral analytics, and real-time alerting.
5. Segment the Network (Micro-segmentation)
Break the network infrastructure into smaller, isolated zones. Each segment has its own rules and policies, reducing the blast radius of any breach.
6. Secure Remote Access
Implement Zero Trust Network Access (ZTNA) to replace traditional VPNs. This enables secure access to specific apps, not the entire network.
Security teams also rely on a cohesive security framework, often aligned with standards like NIST or CISA, to guide decision-making. By combining these layers—identity, monitoring, segmentation, and access control—teams can create a flexible yet resilient trust network access strategy.
What Are the Challenges of Zero Trust Strategy and Implementation?
While the benefits of Zero Trust are clear, implementation isn’t without its obstacles. The shift from perimeter-based security to a Zero Trust strategy requires more than just technology, it demands a fundamental change in how your organization thinks about trust.
One of the biggest hurdles is integrating with legacy systems. Many older applications weren’t built with granular access control or identity-based authentication in mind. Retrofitting these systems to align with Zero Trust principles can be complex and time-consuming.
There’s also a cultural shift involved. Teams that have long relied on firewalls and VPNs may resist new workflows. Security becomes everyone’s responsibility, not just the IT department’s.
Budget constraints add to the challenge. Adopting Zero Trust often means investing in new tools—identity platforms, monitoring solutions, policy engines. Over time, the cost savings from reduced breaches and simplified operations are significant, but the upfront spend can create tool fatigue for smaller teams.
Lastly, maintaining continuous monitoring and enforcing a consistent security posture takes discipline. The model demands constant attention—not a “set it and forget it” approach.
Despite these barriers, the long-term resilience that Zero Trust offers makes the effort worthwhile, especially in a world where threats never stop evolving.
Can Zero Trust Help Mitigate Insider Threats and Supply Chain Risks?
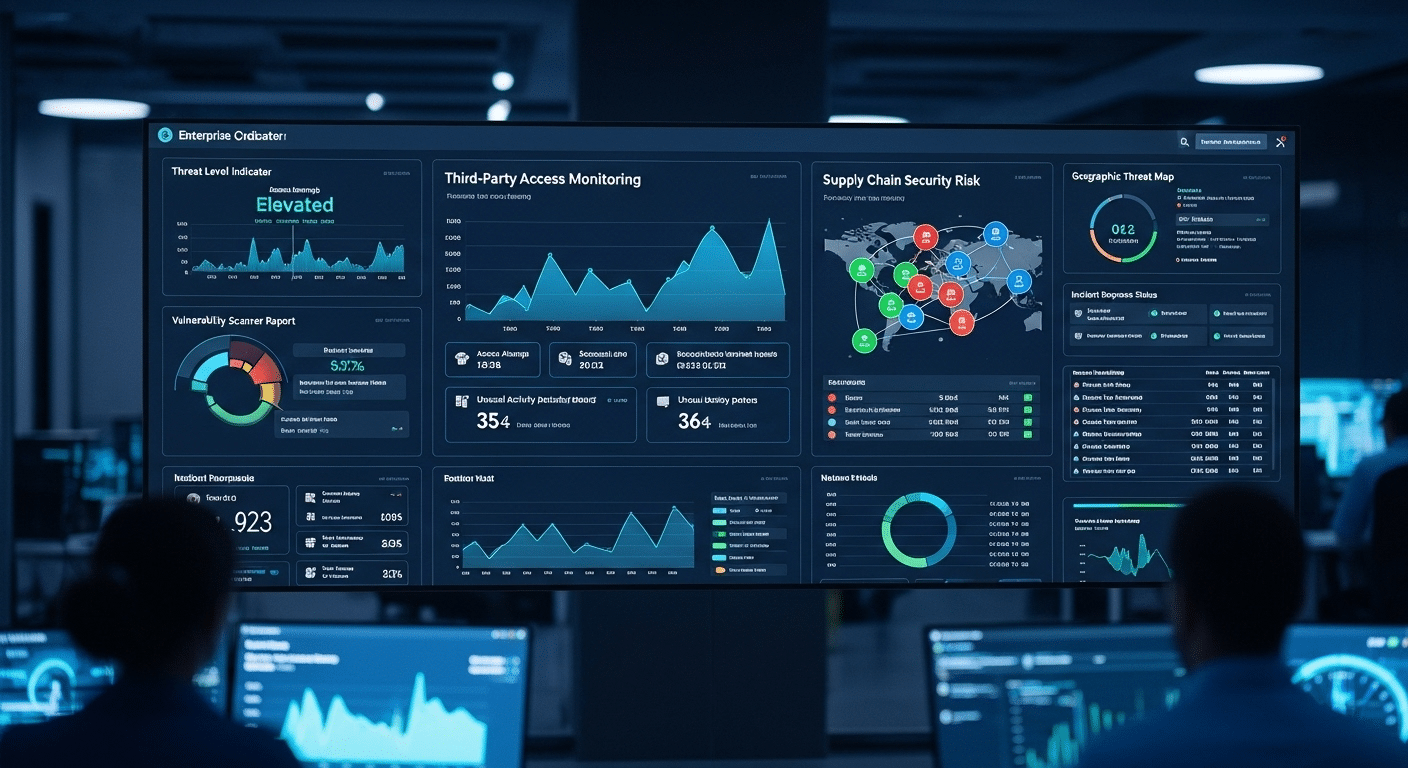
Yes—Zero Trust Security is particularly well-suited to combatting both insider threats and supply chain attacks. That’s because it removes the assumption that any user or system, internal or external—can be trusted by default.
Insider threats often go undetected because traditional models focus protection at the network’s edge. Once inside, malicious actors (or compromised accounts) can move freely. But in a Zero Trust environment, least privilege access ensures that users can only reach what’s essential for their role, nothing more.
In addition, session monitoring and behavioral analytics continuously evaluate how users interact with systems. If someone begins behaving unusually—accessing large amounts of data, or reaching into systems outside their normal scope, the system can flag or terminate access immediately.
This level of scrutiny also extends to external partners and vendors. Many supply chain attacks originate through third-party software or access.
With Zero Trust policies, these connections are sandboxed and monitored. They’re treated with the same skepticism as any other entity requesting access.
By applying the same standards to everyone—internal employees, remote contractors, or third-party vendors, Zero Trust reduces the blind spots that attackers exploit. It’s a proactive way to shrink your attack surface and increase resilience from within.
What Should You Look for in a Zero Trust Platform or Vendor?
Not all Zero Trust platforms are created equal. Choosing the right one means finding a solution that’s not only aligned with the core Zero Trust principles, but also practical for your team to implement and manage.
First, make sure the platform supports ZTNA (Zero Trust Network Access). This replaces traditional VPNs and enables secure access to specific apps, not entire networks.
The platform should also offer strong cloud security features, with support for hybrid and multi-cloud environments.
Look for privilege access controls that are dynamic and adjustable based on real-time risk assessments. Compatibility with modern IT environments—remote workforces, mobile devices, BYOD policies—is also essential.
The best platforms integrate with existing tools for identity management, access control, and threat detection. You want a solution that fits into your existing ecosystem rather than requiring a full overhaul.
Finally, ensure the vendor adheres to a recognized Zero Trust framework (such as those from NIST or CISA) and provides tools for continuous verification of users and devices.
Why Apporto Is a Smart Choice for Zero Trust Implementation
If you’re looking for a platform that checks every one of these boxes, consider Apporto. Built with Zero Trust at its core, Apporto offers seamless ZTNA, robust access controls, browser-based desktops, and support for remote access, all without the complexity of traditional solutions.
Whether you’re a university, mid-sized business, or enterprise, Apporto delivers a simple, secure, and cost-effective way to put Zero Trust into practice.
Final Thoughts
Zero Trust is no longer optional, it’s a necessary shift in how security is approached. As remote work expands and the attack surface grows, relying on old perimeter-based models is no longer sustainable.
Zero Trust offers stronger security, greater flexibility, and reduced breach risk by continuously verifying every user and device. It’s a strategy that fits today’s environments.
Platforms like Apporto make this transition practical. With built-in Zero Trust architecture, secure access, and simple deployment, Apporto helps organizations take the first step confidently.
Start small, think long-term, and build a security posture rooted in trust—earned, not assumed.
Frequently Asked Questions (FAQs)
1. What is the principle of least privilege in Zero Trust?
The principle of least privilege means users only get access to the specific data, apps, or systems they need—nothing more. This limits potential damage if an account is compromised, whether internally or externally.
2. How does ZTNA differ from traditional VPNs?
ZTNA (Zero Trust Network Access) allows access to individual applications, not the whole network. Unlike VPNs, which trust users once connected, ZTNA continuously verifies identity, device health, and context before granting access.
3. Is Zero Trust only for large enterprises or federal agencies?
Not at all. While federal mandates have driven early adoption, Zero Trust is ideal for mid-sized companies, schools, and nonprofits too. Any organization handling sensitive data or supporting remote users can benefit.
4. What’s the first step in a Zero Trust implementation?
Start by mapping your environment—identify users, devices, and critical assets. Then implement strong identity verification, like multi-factor authentication, and apply least privilege access to limit exposure from the start.
5. Can Zero Trust improve cloud security?
Yes. Cloud environments are dynamic and boundaryless, which makes Zero Trust principles essential. By continuously verifying users and securing each access request, you reduce risk across your cloud infrastructure and applications.