You can feel it, even if no one spells it out. Network security does not behave the way it used to. The corporate network is no longer a single building with a guarded door. Remote work scattered users and devices everywhere, and many organizations are still trying to secure something that no longer sits neatly behind a firewall.
So what is zero trust? Zero trust security is a security strategy built on a blunt premise, trust nothing by default. Not the user sitting inside the office. Not the laptop connecting from home. Every request must be verified, inspected, and approved before access is granted.
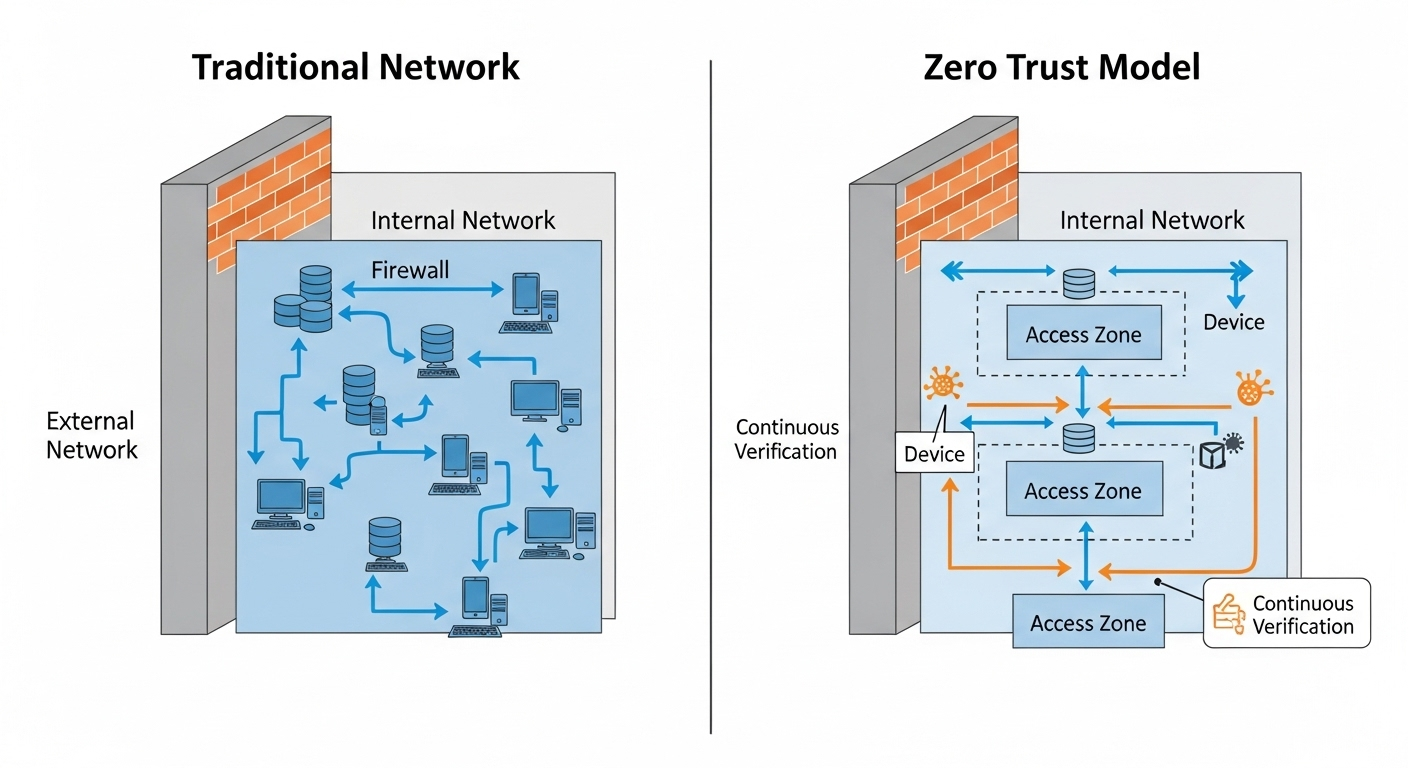
Traditional perimeter based security relied on the castle and moat idea, protect the outside wall and assume everything inside is safe. That assumption aged poorly. If you want a strong security posture today, you need a model that questions every access request.
What Is Zero Trust and Where Did It Come From?
To understand zero trust, you need to start with what it rejects. The zero trust model is a trust security model that refuses to assume safety based on location. It does not matter if a request comes from inside your corporate network or outside it. Access is not granted because someone is “already in.” That idea, implicit trust, is precisely what zero trust principles are designed to eliminate.
The term itself was coined in 2010 by an analyst at Forrester Research. At the time, traditional perimeter based security dominated network security strategy. You built a strong network perimeter, defended it with firewalls and intrusion detection systems, and treated everything inside as trusted. Castle and moat security, that was the metaphor. Keep attackers out, and the interior remains safe.
But attackers rarely stay outside for long. Credentials get stolen. Phishing succeeds. Malware slips in. Once inside, that older trust model allowed broad movement across the entire network.
Zero trust changes the assumption. Every access request is treated as if it originates from an untrusted source. All network traffic, internal or external, must be verified before access is granted. The network itself is no longer considered inherently safe. The focus shifts to protecting individual resources rather than defending a single boundary.
Never trust, always verify. That is not a slogan. It is the foundation of the zero trust security model.
How Is Zero Trust Different from Traditional Network Security?
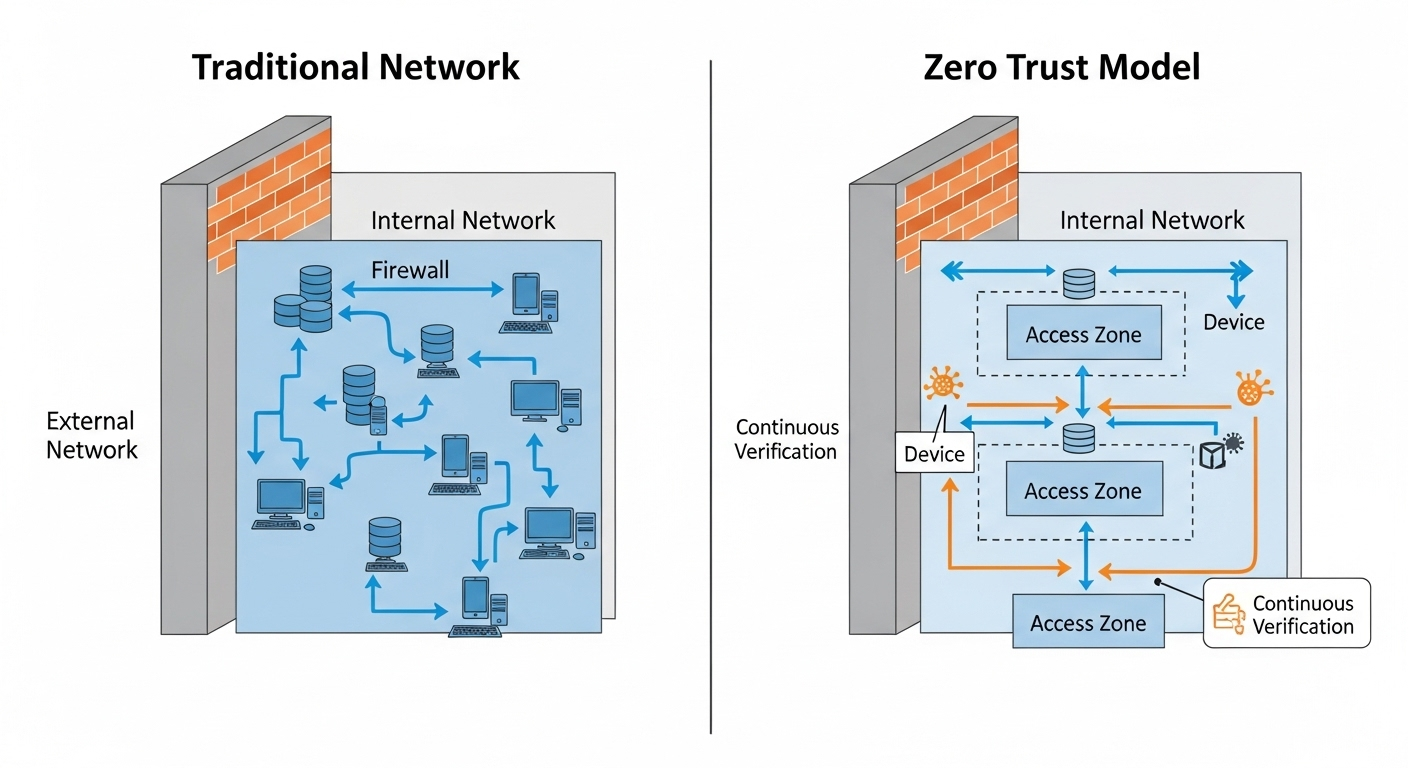
The difference between traditional network security and zero trust architecture is not cosmetic. It is structural. Older models were built around a clear boundary, a network perimeter designed to separate trusted insiders from untrusted outsiders.
Once you crossed that line, access inside the zero trust network was rarely questioned. That approach created a large attack surface, even if it felt secure from the outside.
Zero trust architecture removes the idea of a trusted network edge altogether. There is no automatic trust simply because a user connects through a VPN or sits inside a corporate office.
Every request to access a resource must pass strict access controls, regardless of origin. Trust network access becomes identity based, not location based.
This difference changes how the entire security architecture behaves.
Traditional Perimeter Security vs Zero Trust Architecture
| Traditional Castle-and-Moat Model |
Zero Trust Architecture |
| Trust inside the network |
Trust is never assumed |
| Focus on network perimeter |
Focus on protecting individual resources |
| VPN-based broad access |
Granular, identity-based access |
| Static access controls |
Continuous verification |
| Large attack surface |
Reduced attack surface |
In a zero trust network architecture, lateral movement is deliberately restricted. Even if an attacker gains access to one system, they cannot freely move across the environment. Each step requires re-verification. That containment fundamentally strengthens your security posture.
What Are the Core Principles of Zero Trust?
Once you strip away the marketing language, zero trust is built on a handful of clear principles. They are not abstract theories. They are operational rules that shape how access control, identity validation, and network protection actually work. If you understand these zero trust principles, you understand the model itself.
Here are the foundations that define a zero trust security framework:
- Least-Privilege Access: You grant users only the privilege access necessary to perform their tasks, nothing more. This reduces exposure and helps protect sensitive data by limiting how far a compromised account can reach.
- Continuous Verification: Access is not approved once and forgotten. Every session, every request, is evaluated through continuous monitoring to confirm that the user and context remain legitimate.
- Microsegmentation: The network is divided into smaller zones so that systems and data are isolated. Microsegmentation prevents broad internal access and limits how attackers move between resources.
- Multi-Factor Authentication (MFA): Multi factor authentication requires more than a password, such as a code or biometric verification. This significantly reduces the risk of credential theft leading to full access.
- Device Identity Validation: It is not enough to verify the user. Device identity must also be confirmed, ensuring that only authorized and secure devices can connect.
- Strict Access Control: Access control policies are enforced consistently across systems. No application or service bypasses the rules.
Together, these principles create a disciplined security model. One that reduces risk quietly but effectively, reinforcing your ability to protect sensitive data without relying on outdated assumptions about Zero trust.
How Does Zero Trust Architecture Actually Work?

Understanding the principles is one thing. Seeing how zero trust architecture operates in practice is another. At its core, the model revolves around identity. Access is no longer determined by where you connect from, but by who you are and what you are allowed to access.
Every access request begins with verification. When a user attempts to access resources, the system evaluates user identity, device identity, location, behavior, and context.
Only after these signals are inspected does the system determine whether access should be granted. Even then, granted access is limited to specific applications or data, not the entire private network.
This is where zero trust network access, often called trust network access ZTNA, becomes central. Instead of opening broad tunnels into the organization’s network like traditional VPNs, ZTNA creates secure access to individual services. You connect to what you need, nothing more. The rest of the network remains invisible.
Continuous monitoring then takes over. Zero trust architecture does not stop evaluating risk after login. It reassesses user identity and device security throughout the session. If a device posture changes or suspicious behavior is detected, access can be restricted or revoked in real time.
Traffic is also isolated through microsegmentation. Systems are separated so that even if one component is compromised, attackers cannot easily pivot across hybrid cloud environments or cloud services.
Finally, threat intelligence feeds into the decision engine. Known attack patterns and risk indicators inform policies dynamically. The result is a model that treats every connection as potentially hostile, yet still enables secure access across distributed environments.
Why Is Zero Trust Important for Remote Work and Hybrid Environments?
The corporate network is no longer the center of gravity. Remote work has dispersed users and devices across homes, coworking spaces, airports, and public Wi-Fi. Applications live in cloud platforms. Data flows between services that never touch a traditional office firewall. As a result, organizations rely less on a single, centralized network and more on distributed infrastructure.
That reality weakens older assumptions about trust. When users connect from everywhere, the organization’s network cannot be the primary line of defense. Zero trust provides secure access regardless of location.
It verifies identity and device posture before allowing entry to specific resources, which creates a consistent user experience without compromising control.
This approach also strengthens your ability to protect sensitive data. If credentials are stolen through phishing, attackers cannot automatically move through the environment. Access is limited, validated, and continuously reassessed. The impact of credential theft shrinks.
For hybrid environments, where some systems remain on-premises and others operate in the cloud, zero trust establishes one unified model of verification. That consistency reinforces a strong security posture, even when infrastructure is scattered across multiple platforms and networks.
How Does Zero Trust Reduce Risk and Limit Breach Impact?

No security model can promise absolute prevention. Breaches happen. Credentials leak. Software contains flaws. The real question is containment. How much damage can an attacker cause after gaining entry?
Zero trust is built around limiting that damage. Instead of assuming that internal systems are safe, it treats every connection as potentially hostile. This approach prevents unrestricted movement across the entire organization. If an attacker compromises one account, they do not automatically gain visibility into critical assets or administrative systems.
Microsegmentation plays a central role here. By dividing the environment into smaller, isolated zones, zero trust reduces the blast radius of any breach. Attackers cannot easily pivot from one workload to another. Lateral movement becomes difficult, often impossible without triggering additional verification steps.
This containment strategy also helps defend against insider threats and supply chain attacks. If a trusted vendor account is compromised, access remains limited to only what is explicitly permitted. Sensitive systems remain segmented and protected.
Over time, these layered security measures strengthen your trust security posture. They reduce the attack surface and improve your organization’s ability to respond quickly when anomalies appear. You are not betting everything on a single wall of defense. You are controlling exposure at every step.
Zero Trust reduces risk by:
- Limiting least privilege access
- Isolating traffic
- Enforcing strict user permissions
- Continuous monitoring
The result is not perfect immunity. It is controlled impact, which in practice is far more valuable.
How Does Zero Trust Support Compliance and Regulatory Requirements?
Regulations rarely care about your architecture diagrams. They care about control, visibility, and accountability. Frameworks like GDPR and HIPAA require you to protect sensitive data, restrict access, and document how information moves through your systems. ‘
Federal agencies have also embraced zero trust as a formal security framework, recognizing that perimeter defenses alone cannot satisfy modern compliance expectations.
Zero trust aligns naturally with these requirements. Every access request is authenticated, authorized, and logged. Continuous logging and monitoring provide a detailed record of who accessed what, when, and from which device. That visibility strengthens audit readiness and supports continuous compliance rather than periodic checkbox reviews.
Access management also becomes more precise. Least-privilege policies ensure that users can only reach the data necessary for their roles. If permissions change, policies adjust. If risk signals increase, access can be revoked in real time.
This structured approach reduces ambiguity. You are not relying on broad network trust. You are documenting enforcement. In practice, that clarity improves your ability to demonstrate that sensitive data is protected, not merely assumed to be secure.
What Does Zero Trust Implementation Look Like in Practice?

Zero trust implementation rarely happens overnight. It is a phased effort, sometimes measured in quarters, occasionally in years. You begin by mapping your environment, identifying critical systems, understanding user access patterns, and clarifying which assets require the strongest security control. Without that visibility, policy decisions become guesswork.
A common early step in a zero trust approach is reevaluating VPN usage. Traditional VPNs provide broad access to the network once a user authenticates. Zero trust access replaces that model with granular, application level connectivity.
Users connect only to the specific services they are authorized to use, not the entire environment. Over time, this reduces unnecessary exposure.
Consolidating security tools is another practical objective. Many organizations accumulate overlapping systems, firewalls, endpoint agents, identity platforms, cloud controls. Zero trust encourages integration. Identity, device validation, and policy enforcement work together instead of operating in isolation.
Hybrid cloud environments add complexity, but the model remains consistent. Whether resources reside on premises or in cloud platforms, policies follow the identity, not the location.
Throughout this process, IT teams and security teams must collaborate closely. Implementation is not just a technical upgrade. It requires revisiting user permissions, redefining access boundaries, and aligning operational processes. Done thoughtfully, it strengthens user access control without sacrificing productivity.
What Are Common Challenges When Adopting a Zero Trust Model?
Zero trust sounds simple in theory. In practice, it asks you to rethink habits that have existed for decades. The largest hurdle is cultural. Many teams are accustomed to implicit trust inside the corporate boundary. Removing that assumption can feel restrictive at first, especially when users are used to broad access across the entire network.
Legacy infrastructure creates another obstacle. Older systems were not designed for granular access management or identity based controls. Integrating them into a modern trust model often requires upgrades or careful workarounds.
Mapping user permissions can also be more complex than expected. You must clearly define who needs access to what, and why. Without that clarity, policies either become too permissive or overly restrictive.
Ongoing monitoring is essential. Zero trust is not a one time deployment, it is a living security strategy. Implementation can take years, particularly in large environments, but the improvement in your organization’s ability to manage risk makes the effort worthwhile.
How Does Zero Trust Improve Visibility and Control Across the Entire Organization?

One of the quieter advantages of zero trust is visibility. When every access request is evaluated and logged, you gain insight into how your systems are actually used. Continuous monitoring of network traffic reveals patterns that were once hidden behind broad internal trust. You see who connects, from where, and under what conditions.
Asset inventory awareness improves as well. To enforce precise access control, you must know what resources exist and how they relate to one another. That discipline strengthens your overall security posture. Unknown systems and forgotten accounts become harder to ignore.
Threat intelligence also feeds directly into policy decisions. When new attack techniques emerge, your security model can adapt by tightening controls or flagging suspicious behavior in real time. Instead of reacting days later, you respond quickly.
Over time, this layered visibility improves risk management. You are no longer relying on assumptions about safety. You are observing, measuring, and adjusting based on evidence. That level of control changes how security is practiced across the entire organization.
Why Is Zero Trust Becoming the Standard Security Model for Modern Organizations?
Look at where your applications live. Many run in cloud services. Others remain on premises. Some sit in hybrid cloud environments that blend both. The entire network no longer exists in a single physical space. It is distributed, dynamic, and constantly evolving.
That complexity expands the attack surface. Every new SaaS platform, every external integration, every remote connection introduces another potential entry point. Traditional models built around a fixed perimeter struggle to keep up. You cannot protect what no longer has clear edges.
The zero trust security model addresses this reality by centering on identity rather than location. Access decisions follow the user and the device, not the building or subnet. This trust architecture creates a unified approach to trust security across platforms, clouds, and internal systems.
Organizations rely on identity as the consistent anchor in a fragmented environment. That consistency is why zero trust continues to move from recommendation to expectation.
How Does Zero Trust Compare to VPN-Based Security?
VPNs were designed for a different era. They extend the private network outward, allowing users to connect remotely as if they were physically inside the office. Once connected, broad access is often granted. The assumption is simple, authenticate first, trust afterward.
Zero trust network access works differently. Instead of opening a tunnel into the entire environment, trust network access ZTNA evaluates each access request individually. Users are granted access only to specific applications or services, not to the broader network. Strict access controls remain in place throughout the session, and verification does not stop after login.
The difference is not subtle. One model trusts the connection. The other trusts nothing without proof.
VPN vs Zero Trust Network Access (ZTNA)
| VPN Model |
Zero Trust Network Access |
| Broad network access |
Granular resource-level access |
| Trust once connected |
Continuous verification |
| Larger attack surface |
Reduced attack surface |
| Network-based access |
Identity-based access |
In practice, zero trust reduces unnecessary exposure while still enabling secure connectivity.
How Apporto Delivers Zero Trust Virtual Desktops in Practice

Understanding zero trust in theory is important. Operationalizing it is where most organizations struggle. Policies sound strong on paper, but enforcement often breaks down at the endpoint, especially when remote work and hybrid cloud environments complicate traditional controls.
Apporto virtual desktop platform is built around Zero Trust principles from the ground up. Every user identity and device identity is verified before access is granted. Access is limited to specific applications and resources, not the entire network. Strict access controls and least privilege access are enforced consistently.
Because desktops are delivered through the browser, sensitive data never resides on local devices. That alone reduces risk. Continuous verification monitors sessions in real time, ensuring that trust is not assumed simply because a login succeeded once.
Instead of extending a private network outward through VPN tunnels, Apporto applies zero trust network access directly to the desktop experience. You gain secure access without expanding your attack surface.
The result is practical zero trust security, not just policy language. A controlled environment that protects sensitive data while maintaining performance and usability.
Conclusion
At this point, the pattern is clear. What is zero trust if not a disciplined commitment to verification over assumption? It replaces inherited internal trust with identity based control. It relies on continuous verification instead of static approvals.
The perimeter no longer defines safety. Identity does. Context does. Device health does.
Zero trust is not a theoretical upgrade to your security strategy. It is a practical framework designed to protect sensitive data across distributed systems, hybrid cloud environments, and remote access scenarios. The question is no longer whether the model makes sense. It is whether your current security architecture reflects it.
If you are evaluating how to move from concept to execution, especially in virtual desktop environments, it may be time to see what a zero trust approach looks like in action. Explore Apporto Virtual Desktop.
Frequently Asked Questions (FAQs)
1. What is zero trust in simple terms?
Zero trust is a security model built on one clear rule, never assume trust. Every user, device, and access request must be verified before permission is granted. It removes automatic internal trust and relies on identity, context, and continuous verification to protect systems and data.
2. How does zero trust architecture work?
Zero trust architecture evaluates each access request based on user identity, device health, and risk signals. Access is granted only to specific resources, not the entire network. Continuous monitoring ensures permissions remain valid throughout the session, limiting exposure and enforcing least privilege access.
3. Is zero trust only for large enterprises?
No. While large enterprises often lead adoption, zero trust applies to organizations of any size. Smaller companies also face phishing, insider threats, and credential theft. A structured security model built around identity and verification improves protection regardless of scale.
4. Does zero trust replace VPNs?
In many cases, yes. Zero trust network access replaces traditional VPN tunnels with application specific access. Instead of broad network entry, users connect only to authorized services. Continuous verification reduces the attack surface and strengthens overall security controls.
5. How long does zero trust implementation take?
Implementation timelines vary. Smaller environments may transition within months, while complex enterprises may require years. Zero trust is not a single product deployment. It is an evolving strategy that gradually strengthens access control and monitoring practices.
6. Is zero trust required for compliance?
Regulations rarely mandate zero trust by name, but many compliance frameworks require strict identity verification, access management, and monitoring. Zero trust supports these objectives naturally, making it easier to demonstrate control over sensitive data.