What is a cyber range, and why are so many organizations suddenly talking about it as if it were essential infrastructure rather than optional training? At its core, a cyber range is a controlled, virtual environment designed to simulate real-world networks, systems, and cyber threats.
It allows cybersecurity professionals to train, test defensive strategies, and rehearse responses to attacks without putting actual systems at risk. Think of it as a proving ground for digital defense, a place where mistakes are allowed and lessons are absorbed without consequence.
The urgency is not accidental. The cybersecurity workforce gap continues to widen, even as evolving cyber threats grow more sophisticated and persistent. Ransomware, supply chain compromises, and targeted intrusions no longer feel rare. They feel routine.
Cyber range training has emerged as a practical response. Organizations use these environments to sharpen skills, validate security controls, and prepare teams for realistic attack scenarios.
In this blog post, you will see how cyber ranges work behind the scenes, who relies on them, what benefits they deliver, where limitations exist, and why they increasingly play a role in compliance and workforce development strategies.
What Is a Cyber Range in Simple Terms?
A cyber range is a simulated environment where you practice defending against cyber attacks without putting real systems in danger. It mirrors real world networks, but nothing inside it touches your actual production systems.
Think of it like a physical shooting range. Law enforcement officers do not practice in crowded streets. They train in controlled spaces designed for repetition, error, and refinement. A cyber range follows the same logic. You rehearse digital defense in a controlled environment that absorbs mistakes safely.
Safe failure is the point. You can misconfigure a firewall, overlook a threat, or respond too slowly, and the only consequence is a lesson learned. No customer data is exposed. No real servers are damaged. The isolated environment protects live infrastructure while still feeling authentic.
A cyber range consists of layered components that recreate realistic attack scenarios. It separates training systems from actual systems, ensuring exercises remain contained. That separation allows teams to experiment, adjust defensive strategies, and improve without operational disruption.
Core Components of a Cyber Range
- Simulated environment replicating real world networks
- Target infrastructure representing actual systems
- Security tools for detection and response
- Virtualization layer supporting virtual instances
- Orchestration layer coordinating exercises
How Does a Cyber Range Actually Work?
Behind the interface, a cyber range runs on virtualization technologies that carve multiple virtual environments out of shared hardware. Instead of building a separate physical lab for every scenario, the platform creates virtual machines that behave like real servers, firewalls, endpoints, and databases. These simulated systems sit on an underlying infrastructure, often housed in a secure data center or cloud cluster.
The phrase software defined virtual infrastructure sounds dense, but the idea is simple. Hardware becomes flexible. Storage infrastructure, networking, and computing resources are abstracted into software controls. That means you can spin up entire real world networks in minutes, replicate corporate infrastructures, or dismantle them just as quickly.
An orchestration layer acts as the conductor. It coordinates which virtual machines are deployed, which attack scenarios are launched, and how traffic flows between components. Realistic network traffic is injected to mimic normal user behavior, background noise, and suspicious patterns. Trainees are not defending a blank screen, they are navigating an environment that feels convincingly alive.
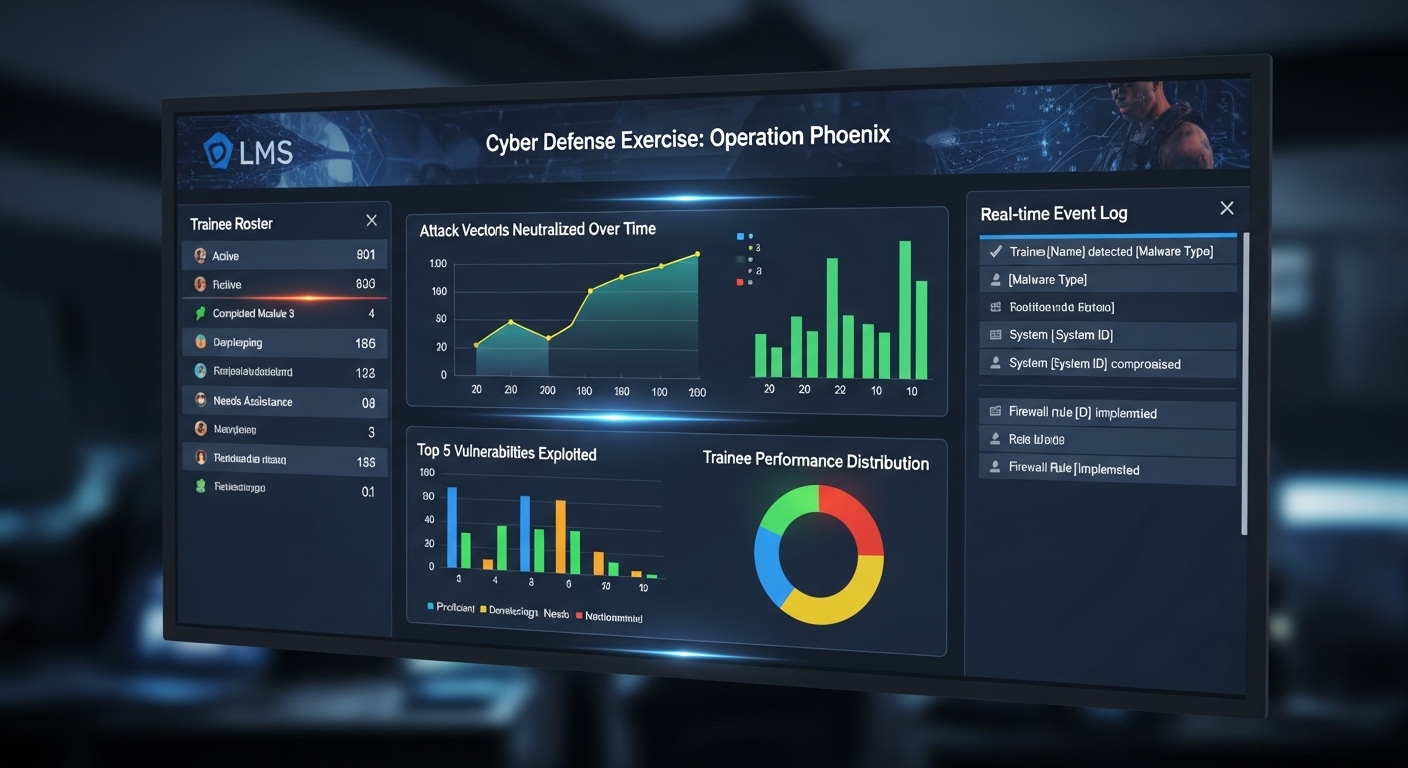
Learning management system integration often tracks progress, logs performance metrics, and ties exercises to structured coursework. In advanced setups, resources scale dynamically. If an exercise requires more virtual instances or heavier load simulation, the environment expands automatically.
You are not just observing theory. You are operating inside a controlled replica of reality, shaped to test your decisions in ways that feel uncomfortably real, which is precisely the point.
What Types of Cyber Ranges Exist?
Not all cyber ranges are built the same. Some are streamlined for training fundamentals. Others replicate enterprise networks with unnerving precision. The differences matter, especially when your objectives vary from workforce development to advanced red team exercises.
Simulation ranges are often the starting point. These environments rely on abstracted attack scenarios rather than full system replication. They focus on logic, workflow, and defensive strategy inside a contained virtual environment. Good for building foundational cybersecurity skills.
Emulation ranges go further. They recreate real world attack scenarios by replicating actual systems, network configurations, and traffic patterns. Advanced SOC teams use them to practice against realistic adversary behavior. The environment behaves like a live network because, in many ways, it mirrors one.
Overlay ranges layer simulated attacks over existing enterprise networks. They allow testing without fully rebuilding infrastructure. Hybrid ranges combine elements of simulation and emulation, offering flexibility for complex enterprise networks.
Then there are SaaS cyber range platforms, cloud-hosted and accessible without heavy on-prem buildouts. Educational institutions and smaller organizations often prefer these for cost efficiency and ease of deployment. Open-source builds also exist, offering customizable frameworks for organizations with technical depth.
Below is a clearer breakdown.
Comparison Table: Types of Cyber Ranges
| Type | Description | Best For | Deployment Model |
|---|---|---|---|
| Simulation Range | Abstracted attack simulations | Foundational training | SaaS / On-prem |
| Emulation Range | Realistic replication of actual network | Advanced SOC teams | On-prem / Hybrid |
| Overlay Range | Layered over live systems | Enterprise testing | On-prem |
| Hybrid Range | Mix of simulation and emulation | Complex enterprise networks | Hybrid |
| SaaS Cyber Range | Cloud-hosted platform | Education & SMB | SaaS |
Why Are Cyber Ranges Important for Modern Security Teams?

Security teams rarely struggle because they lack theory. They struggle because real incidents unfold fast, unpredictably, and under pressure. That is where cyber range exercises become essential.
Hands-on skill development builds instinct. When you repeatedly encounter realistic attack techniques inside a simulated environment, defensive strategies stop being abstract concepts and start becoming reflexes.
Red Team versus Blue Team exercises sharpen that instinct further. One group launches simulated attacks, the other detects and responds. It feels competitive. It is also deeply instructive.
The data supports the practice. Teams that train in ranges often improve incident response times by 40 to 50 percent compared to those who rely solely on classroom instruction. Memory retention from immersive training can reach 75 percent, far above the modest 5 percent associated with passive learning. Those improvements influence metrics such as Mean Time to Detect and Mean Time to Contain.
Coordinated incident response also improves. Teams learn to communicate under pressure, delegate tasks, and validate security posture in a safe but demanding environment.
What Cyber Ranges Provide
- Safe environment to practice defending
- Real life cyber attacks simulation
- Risk management training
- Defensive strategies testing
- Threat detection improvement
- Muscle memory development
Who Uses Cyber Ranges and Why?
Cyber ranges are not reserved for one niche audience. Their adoption spans sectors where security failure carries serious consequences. Government agencies rely on cyber ranges to prepare teams for national defense and digital resilience.
Some governmental organizations go further, using them to train specialists in cyber warfare tactics, ensuring readiness against state-sponsored threats. The stakes are high, and rehearsal in a controlled environment reduces uncertainty.
Critical infrastructure sectors, including energy, utilities, and transportation, use cyber ranges to test defensive strategies without risking operational technology. A misstep inside a live grid system is unacceptable. Practice must happen elsewhere.
The financial sector invests heavily in simulation ranges to protect sensitive transactions and customer data. Rapid detection and containment matter when seconds can translate into millions. Healthcare systems, managing patient records and life-critical systems, use ranges to strengthen response protocols while preserving compliance.
Corporate security teams employ cyber ranges to validate enterprise defenses and sharpen coordinated incident response. Educational institutions integrate them into cybersecurity education programs, preparing the next generation of professionals with hands-on experience rather than theoretical exposure alone.
Ethical hackers and red team specialists use these environments to refine attack and defense techniques. For many organizations, cyber ranges also serve recruitment and retention goals, signaling commitment to developing a resilient cybersecurity workforce.
How Do Cyber Ranges Support Compliance and Risk Management?

Compliance is rarely about good intentions. It is about proof. Regulators and auditors want evidence that your security program is not theoretical, that your teams can respond to real incidents under pressure. Cyber ranges help you demonstrate that readiness in concrete ways.
Because exercises are structured and repeatable, they generate demonstrable training records. Participation logs, performance metrics, and scenario outcomes can be documented and reviewed during audits. That matters in sectors like energy, healthcare, and finance, where compliance requirements are strict and continuous.
Cyber ranges also allow you to rehearse data breaches before they happen. Instead of waiting for a real incident to test your procedures, you simulate one. You observe how your team reacts, how quickly threats are detected, and whether communication channels hold up. Weaknesses surface early. That is a gift, not a failure.
Safe experimentation plays a role as well. You can introduce new security tools, adjust configurations, or test policy changes without disrupting live security infrastructure. Risk management becomes proactive rather than reactive.
In many organizations, the range becomes an internal audit tool, quietly validating whether defensive claims match operational reality.
What Are the Limitations or Challenges of Cyber Ranges?
For all their strengths, cyber ranges are not frictionless. Advanced platforms can require significant upfront investment, particularly when organizations build on-prem environments supported by physical infrastructure. Servers, storage, networking hardware, all of it adds up. Cloud-based options reduce some of that burden, but cost never disappears entirely.
Building realistic attack scenarios is another challenge. Sophisticated attacks evolve constantly. Crafting simulations that accurately reflect current tactics requires expertise, time, and continuous updates. Without careful design, exercises risk becoming predictable.
Skilled instructors or facilitators are essential. A range without guidance can turn into a technical playground rather than structured development. Security teams need context, feedback, and performance evaluation to improve meaningfully.
There is also the question of realism. No simulated system can perfectly mirror the unpredictability of live incidents. Over-simulation may create a sense of preparedness that feels stronger than it actually is.
Potential Challenges of Cyber Range
- Requires skilled facilitation
- Can be resource intensive
- Needs continuous scenario updates
- May not replicate every evolving threat
- Integration into enterprise security program
How Do Cyber Ranges Compare to Traditional Cybersecurity Training?
Traditional cybersecurity training has long relied on classroom learning and static labs. You complete controlled exercises on preconfigured systems. That approach builds foundational knowledge, but it rarely captures the urgency or unpredictability of real world cyber threats.
Static labs often follow scripted paths. You know what is coming next. The environment does not adapt to your decisions. Mistakes are corrected quickly, sometimes before they even sink in. Skill retention in those settings tends to be modest, often around five percent for purely theoretical instruction.
Live cyber range simulations feel different. They recreate realistic scenarios inside dynamic training environments. You encounter unexpected behavior, shifting attack techniques, and time pressure. Safe failure allows you to experiment, but the experience still carries weight. Retention improves significantly, in some cases reaching seventy-five percent when learning is immersive and interactive.
The difference is not subtle. One approach teaches concepts. The other conditions responses.
Comparison Table
| Feature | Traditional Training | Cyber Range |
|---|---|---|
| Realistic Scenarios | Limited | High |
| Safe Failure | Low | High |
| Team Exercises | Minimal | Extensive |
| Skill Retention | ~5% | Up to 75% |
| Incident Simulation | Theoretical | Practical |
Are Cyber Ranges the Future of Cybersecurity Workforce Development?

The cybersecurity workforce gap is no longer a distant concern. It is measurable, persistent, and growing. Organizations struggle to fill cybersecurity positions while cyber attacks increase in scale and sophistication. That imbalance creates pressure. And pressure demands better preparation.
Hands-on experience has become the dividing line. Employers want professionals who can navigate real systems, interpret threat signals, and act decisively under uncertainty. Reading about evolving challenges is no longer enough. You must practice responding to them.
Enterprise networks face constant probing, automated scanning, and targeted intrusion attempts. Security teams cannot afford hesitation. Cyber ranges offer a structured way to build that readiness before incidents occur. Through repeated exercises, teams improve detection, refine response playbooks, and strengthen collaboration.
Adoption is expanding across industries. Financial institutions, healthcare systems, government agencies, and educational programs increasingly view range-based training as foundational rather than optional. It supports enterprise readiness in ways traditional instruction struggles to match.
Will cyber ranges replace all forms of training? Unlikely. But as cyber attacks continue to grow in complexity, immersive environments are becoming central to developing a resilient cybersecurity workforce prepared for what comes next.
Final Thoughts
When you step back, the value becomes clearer. A cyber range offers something difficult to replicate elsewhere, a secure environment where your teams can practice realistic attack techniques without endangering live systems. You test defensive strategies, rehearse incident response, and document training outcomes that support compliance goals.
Cyber ranges are important because preparation cannot rely on theory alone. Still, they are not effortless investments. Cost, complexity, and ongoing scenario updates require planning. Without clear objectives, even the most advanced platform can become underused.
The real question is not whether cyber ranges matter. It is whether your current security maturity justifies immersive practice. If your organization handles sensitive data, operates critical systems, or faces constant exposure to cyber threats, structured simulation deserves serious consideration.
Frequently Asked Questions (FAQs)
1. What is a cyber range used for?
A cyber range is used for cybersecurity training, testing, and research. It allows security teams to practice defending against cyber attacks, validate defensive strategies, and improve incident response in a controlled environment without risking live systems or production networks.
2. How does a cyber range simulate real world cyber attacks?
A cyber range recreates real world networks using virtual machines and simulated systems. It injects realistic attack techniques, malicious traffic, and evolving threat scenarios into an isolated environment, allowing participants to detect, analyze, and respond as if facing actual cyber threats.
3. Are cyber ranges only for government agencies?
No, cyber ranges are widely used beyond government agencies. Financial institutions, healthcare providers, critical infrastructure operators, educational institutions, and corporate security teams rely on them to strengthen cybersecurity skills and improve organizational readiness against sophisticated attacks.
4. How do cyber ranges improve incident response time?
By repeatedly practicing coordinated incident response in realistic scenarios, security teams build familiarity and muscle memory with their tools. This hands-on experience often leads to faster threat detection and containment during real incidents.
5. What industries benefit most from cyber range training?
Industries that manage sensitive data or critical systems benefit most. This includes healthcare, finance, energy, transportation, government, and large enterprises that require advanced threat detection and validated defensive strategies.
6. Can small businesses use cyber range platforms?
Yes, many modern cyber range platforms offer cloud-based options designed for smaller organizations. These scalable solutions provide affordable access to immersive training without requiring large investments in physical infrastructure.

