Step into any airport lounge or corner café and you’ll see it, dozens of people tethered to public Wi Fi networks as if they were harmless utilities, like tap water or overhead lights. Convenient, yes. Safe, not always.
Your internet connection, when left unguarded, quietly exposes browsing history, online identity, and patterns of internet traffic that say more about you than you might expect.
At the same time, remote employees now log into company systems from spare bedrooms, hotel rooms, sometimes even parked cars. Remote access has become ordinary. That familiarity can blur the risks. Sensitive data moves across open networks every day, payroll records, client contracts, internal communications. And most internet users assume their internet service provider handles the heavy lifting of network security. It does not.
This is where understanding how VPN works becomes less technical trivia and more practical literacy. A virtual private network creates a secure connection by routing your internet traffic through an encrypted path to a remote server.
That simple redirection helps protect data, conceal your IP address, and reduce tracking from third parties. Privacy is not paranoia. It is maintenance. And knowing how a VPN works is part of that maintenance.
What Is a Virtual Private Network, VPN, in Simple Terms?
Strip away the jargon and a virtual private network is exactly what the name suggests, a private pathway carved out of a very public system. The internet is, by design, open. Your internet connection routes data across shared network infrastructure owned by telecom companies, data centers, and service operators you will never meet. That openness is efficient. It is not private.
A virtual private network creates a sealed corridor inside that openness. Instead of sending data directly through your internet service provider to its final destination, a VPN service reroutes your traffic first to a VPN server operated by a VPN provider. That server becomes an intermediary, a checkpoint, sometimes even a disguise.
Here is the distinction that matters. Your internet service provider gives you access to the internet. It controls the physical wires, fiber lines, and wireless signals that connect your device to the broader network infrastructure. A VPN provider, on the other hand, overlays vpn technology on top of that connection. It does not replace your internet service provider. It wraps around it.
When you connect to a vpn server, your traffic passes through that server before reaching websites, apps, or company systems. To outside observers, the traffic appears to originate from the vpn server rather than your original location. That redirection is not cosmetic. It changes how your internet connection is seen, logged, and tracked.
In simple terms, a virtual private network turns a public route into a controlled one. You still travel the same internet. You just take a quieter road.
How VPN Works Step by Step & What Actually Happens When You Connect to it?
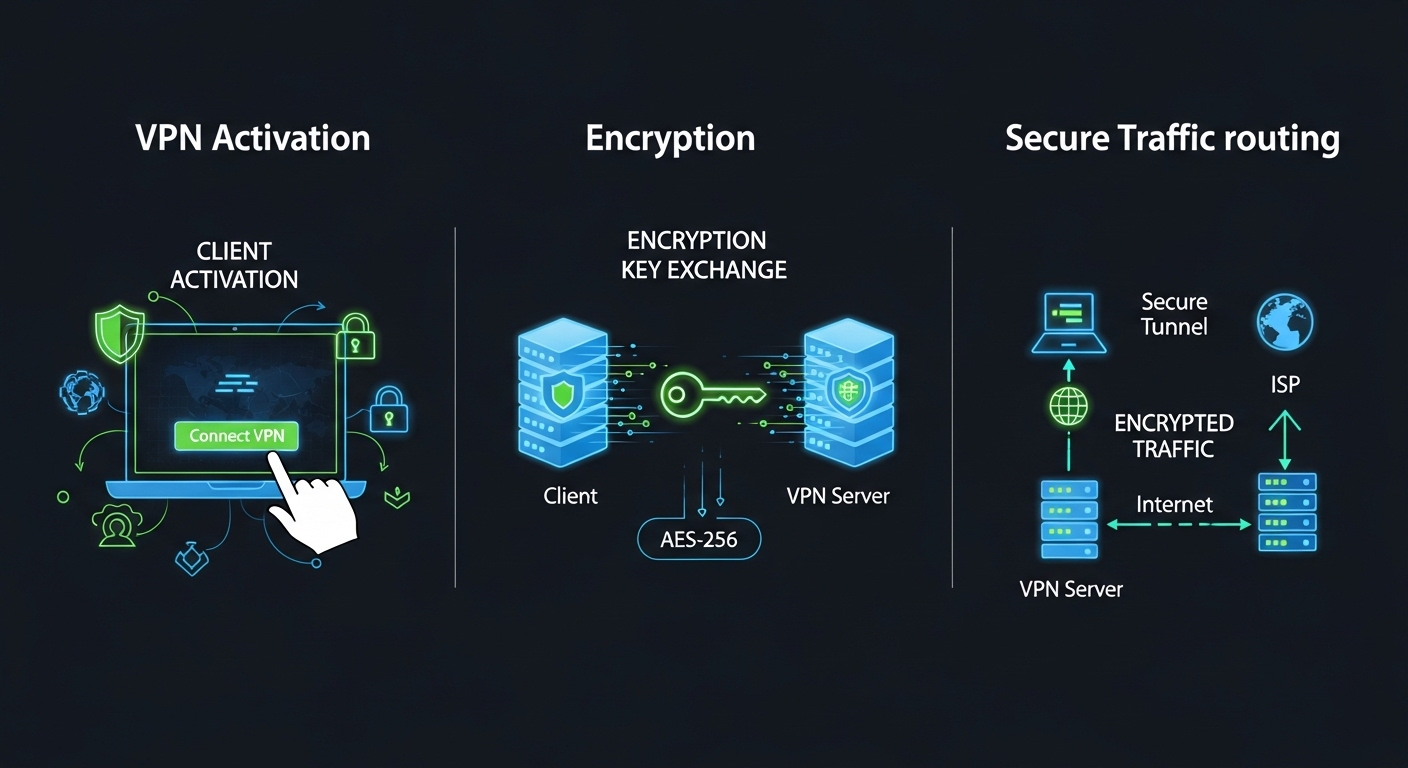
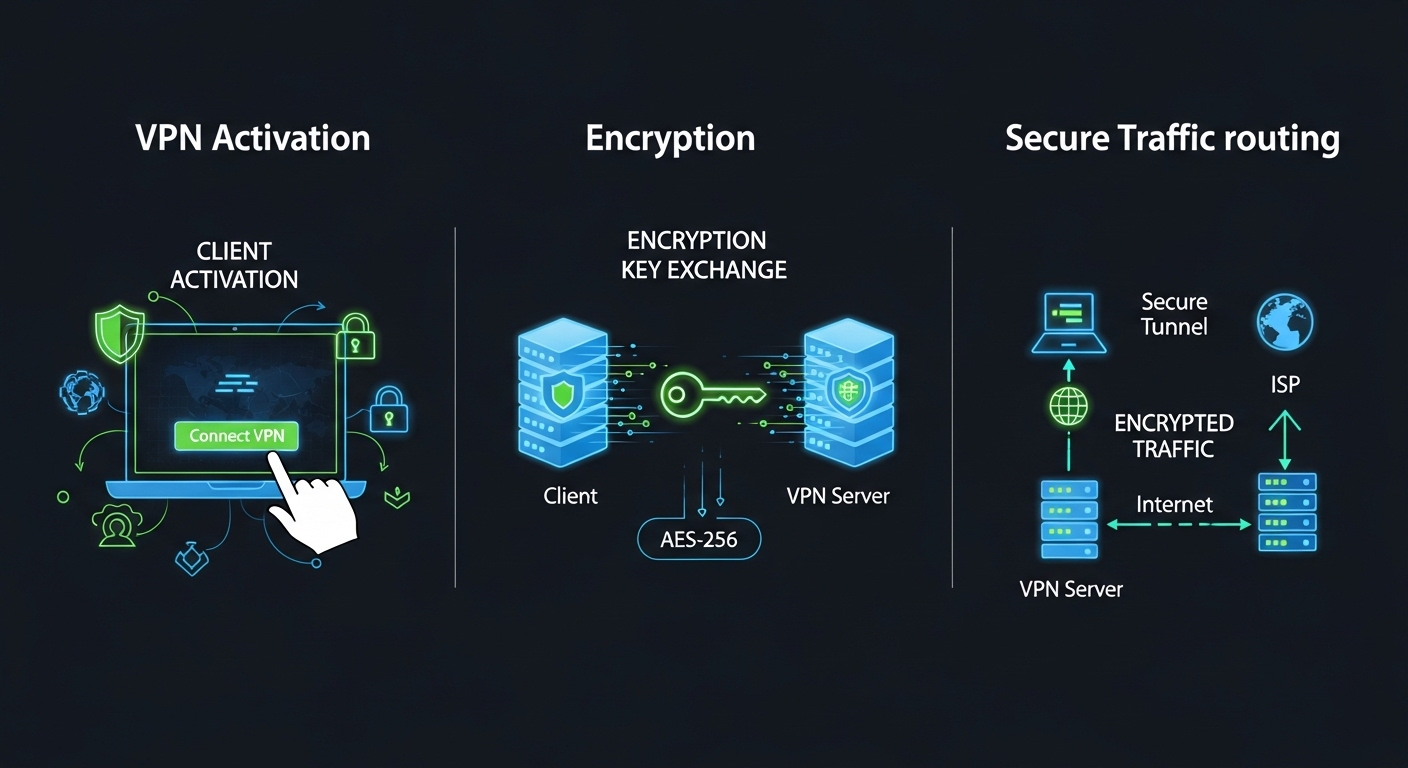
You tap “connect” and it feels instant. Behind that small click, however, several coordinated actions unfold in seconds. Understanding how VPN works means slowing that moment down and examining what actually takes place between your device and the wider internet.
First, your device activates vpn client software. That software is not just a button interface. It handles authentication, negotiates encryption protocols, and prepares your system to build a secure link. Once activated, it reaches out across your existing internet connection to establish a vpn connection with a remote server operated by your chosen provider.
When that remote server responds, something important happens. The vpn encrypts your outgoing data before it leaves your device. An encryption key is generated and shared securely between your device and the vpn server. This key scrambles your internet traffic into unreadable code, creating what is often described as an encrypted vpn tunnel. Anyone attempting to intercept vpn traffic at this stage sees distorted data, not usable information.
At the same time, your original ip address is concealed. Instead of websites seeing the location assigned by your internet service provider, they see the ip address of the remote server. From the outside, your activity appears to originate from that server’s location.
Once the encrypted data reaches the vpn server, it is decrypted using the matching encryption key. The server then forwards your request to its intended destination. Responses from websites or applications travel back through the same encrypted tunnel, protecting data transfers on the return trip.
It sounds complex. In practice, it happens quietly, repeatedly, every time you load a page or send a file.
To make it clearer, here is the sequence in order:
- VPN client software initiates the request: Your device activates the vpn client and begins establishing a secure vpn connection over your existing internet connection.
- VPN connection to remote server: The client authenticates with a remote server managed by the vpn provider, preparing to route vpn traffic through that server.
- Encrypted VPN tunnel creation: An encrypted tunnel is formed using shared encryption keys, allowing data to travel securely between your device and the vpn server.
- IP address masking: Your real ip address is hidden, and the remote server’s ip address becomes visible to external websites and services.
- Internet traffic routed through VPN server: All internet traffic passes through the remote server before reaching its final destination.
- Data decrypted at destination: The vpn server decrypts outbound data before forwarding it, and encrypts incoming responses before sending them back to you.
This is how a vpn encrypts, redirects, and shields your activity.
What Is a VPN Tunnel and Why Is It So Important?
The phrase “VPN tunnel” sounds abstract, almost theatrical. In reality, it describes something quite precise. A vpn tunnel is a secure, encrypted pathway between your device and a remote server. Instead of broadcasting your data openly across shared network routes, your information travels through an encrypted connection that shields it from inspection.
Think of ordinary internet traffic as postcards. Anyone handling them along the route can glance at the message. A vpn tunnel transforms those postcards into locked containers. The tunneling protocol is the mechanism that builds that container.
It determines how data packets are wrapped, transported, and verified as they move across networks. Inside that secure tunnel, encryption processes scramble the data into unreadable code. Only the intended recipient, holding the correct encryption key, can reverse that scrambling.
When a VPN encrypts data, it does not simply hide content. It restructures it. The encrypted vpn tunnel ensures that even if someone intercepts your data mid-transfer, what they capture is useless noise. That is why a vpn tunnel matters. It protects sensitive data during transmission, not just at rest.
The difference becomes clearer when placed side by side:
| Without VPN |
With VPN Tunnel |
| Data travels openly through shared network routes |
Data travels inside an encrypted VPN tunnel |
| Internet service providers can view traffic patterns |
Traffic appears encrypted and unreadable |
| Higher exposure to interception on public networks |
Secure tunnel reduces interception risks |
| IP address directly visible to external services |
IP address masked by remote server |
How Does a VPN Encrypt Your Data?

Encryption is the spine of VPN technology. Without it, a virtual private network would simply reroute traffic, not protect it. When a VPN encrypts your data, it transforms readable information into coded text that cannot be understood without the correct key. That transformation happens before your data leaves your device.
Encryption protocols define the rules of that transformation. These protocols determine how data is scrambled, how encryption keys are exchanged, and how integrity is verified during transmission. Strong encryption protocols prevent tampering, impersonation, and unauthorized access.
One of the most widely used standards is the Advanced Encryption Standard, often referred to as AES 256-bit. The number refers to the length of the encryption key.
Longer keys create exponentially more possible combinations, making brute-force decryption attempts practically impossible with current computing power. When your VPN uses AES, your internet traffic becomes mathematically protected.
Internet Protocol Security, commonly called IPSec, is another widely adopted framework. It operates at the network layer and encrypts data packets before they travel across networks.
Secure Socket Tunneling Protocol, or SSTP, wraps traffic inside SSL encryption, the same protective layer used for secure websites. These mechanisms differ in structure, but their objective remains the same, to secure sensitive data.
Encryption relies on keys. A public key encrypts outgoing data, and a matching private key decrypts it. In many systems, only authenticated users who possess the correct credentials can access these keys. That restriction ensures that encrypted traffic remains private.
Common VPN protocols explained simply:
- OpenVPN: A widely trusted protocol known for flexibility and strong encryption, often using AES and open-source auditing for transparency.
- IKEv2: A fast and stable protocol, particularly useful for mobile devices that switch between networks while maintaining secure connections.
- SSL VPN: Uses secure socket layer encryption to protect traffic, often accessed directly through web browsers without complex setup.
- SSTP: Secure Socket Tunneling Protocol, integrates with certain operating systems and uses strong SSL encryption for data protection.
What Happens to Your IP Address When You Use a VPN?
Your IP address is more revealing than most people realize. It identifies your general location, your internet service provider, and in many cases, patterns tied to your online identity. Every time you request a webpage, stream a video, or access resources online, that IP address travels with the request.
When you connect to a VPN, that dynamic changes immediately. Instead of your user’s IP address appearing as the origin of your activity, the vpn server’s IP address takes its place. Websites, apps, and external services no longer see your direct connection. They see the address assigned to the remote server handling your traffic.
This masking serves two practical functions. First, it enhances privacy. Your actual location becomes obscured, reducing the ability of third parties to track browsing behavior or build profiles tied to your physical region. Second, it enables location spoofing.
By selecting a vpn server in another country or city, you can appear to connect from that region. That capability allows you to gain access to region-restricted content, bypass certain geographic limitations, and test services as if you were elsewhere.
It is important to understand the boundary here. A VPN changes how your IP address is presented to external systems. It does not erase your identity from every database, nor does it guarantee anonymity. It simply interposes a remote server between you and the broader internet access environment.
Your IP address does not disappear. It is redirected. And that redirection alters who can see what.
What Are the Three Main Types of VPNs?

Not all VPNs serve the same purpose. The underlying encryption principles may look similar, but the architecture and intended use vary depending on who needs secure access and how that access is structured. Broadly speaking, VPN solutions fall into three main categories, remote access VPNs, site to site VPNs, and mobile VPNs. Each addresses a different operational need within a network infrastructure.
Understanding these types helps you see where a VPN fits, not just for personal privacy, but for structured network resources and business continuity.
What Is a Remote Access VPN?
A remote access VPN is the most familiar model for many remote users. It allows individuals to connect securely to a corporate network from outside the physical office. Remote employees use this type of remote access VPN to log into company resources, access internal systems, and interact with files stored behind corporate firewalls.
Here, the user’s device runs client software that establishes an encrypted connection to the organization’s network. Once authenticated, the user can access resources as though physically present inside the office local network. This structure protects sensitive data while allowing flexibility. For distributed teams, consultants, and hybrid workers, remote access VPNs function as a controlled gateway into protected environments.
What Are Site-to-Site VPNs and When Are They Used?
Site to site VPNs operate at a broader level. Instead of connecting individual remote users, they link entire networks together. A local network in one office connects securely to another local network in a different location, forming a unified company’s network infrastructure.
This model is common in larger organizations with multiple branches or data centers. Rather than managing separate connections for each user, the networks themselves establish a permanent encrypted bridge. Employees in one office can access network resources hosted in another without exposing traffic to public internet routes. Site to site VPNs emphasize infrastructure stability rather than individual mobility.
How Do Mobile VPNs Work?
A mobile VPN addresses a specific challenge, unstable connectivity. Mobile devices frequently switch between Wi Fi, cellular data, and other internet connected devices. Traditional VPN sessions can drop during these transitions. A mobile VPN maintains session continuity even when the underlying network changes.
This matters for professionals who rely on multiple devices throughout the day. Field workers, delivery teams, healthcare staff, and on-call engineers depend on stable, secure connections while moving between locations. A mobile VPN preserves authentication and encrypted communication during these network changes.
The key distinction lies in adaptability. While remote access VPNs focus on connecting users to a corporate network and site to site VPNs focus on linking infrastructure, mobile VPNs prioritize session persistence and resilience across shifting connectivity conditions.
How Does a VPN Protect You on Public Wi-Fi?
Public Wi Fi networks feel convenient, almost invisible. You connect, the page loads, life moves on. What you do not see is how exposed that connection can be. Unlike a secured home network, many public access points lack strong security measures. Traffic moves across shared channels, and those channels can be monitored.
One of the most common threats on public Wi Fi networks is the so-called man in the middle attack. In simple terms, an attacker positions themselves between you and the network. Instead of your data traffic moving directly to its destination, it passes through an unauthorized device first. Passwords, account credentials, even financial information can be intercepted if no encryption is in place.
This is where a VPN protects you. When you activate a VPN, your device creates a secure connection before any meaningful data traffic leaves your system. That connection encrypts sensitive data at the source. Even if someone attempts to intercept the transmission, the information appears scrambled and unreadable.
Encryption changes the risk profile entirely. Without it, data sent over open networks can be observed in plain form. With it, private data becomes coded text that cannot be interpreted without the proper key. That distinction is crucial in places where network administrators are unknown and infrastructure oversight is minimal.
A VPN does not make public Wi Fi flawless. It adds a protective layer. It creates secure access where none existed. In environments designed for convenience rather than protection, that layer matters more than most people realize.
Can a VPN Prevent ISP Tracking and Bandwidth Throttling?

Your internet service provider sits at a powerful vantage point. Every website you visit, every streaming session, every file download passes through its network infrastructure.
That visibility allows an internet service provider to observe patterns in your browsing history and categorize network traffic by type. In some cases, traffic linked to streaming or gaming can be intentionally slowed, a practice known as bandwidth throttling.
A VPN changes what your ISP can see. When a VPN works correctly, it encrypts data before it leaves your device and routes it through a remote server.
Instead of your provider seeing specific websites or application types, it sees encrypted network traffic traveling to a single destination, the VPN server. The contents and categories of that traffic are obscured.
Because the ISP cannot easily identify whether you are streaming video, transferring files, or accessing a specific service, targeted throttling becomes more difficult. The ISP still sees that data is moving, but it cannot distinguish the type of activity inside the encrypted channel.
This does not guarantee faster speeds in every situation. The VPN itself can introduce slight overhead due to encryption. However, for many internet users, using a VPN can reduce intentional slowdowns tied to traffic classification and limit how much browsing history is directly observable by their provider.
How Do Businesses Use VPNs for Secure Remote Access?
In most organizations, the corporate network contains more than shared folders. It houses financial systems, customer databases, internal communications, and proprietary tools that are not meant for public exposure. When remote employees need to connect from outside the office, that access must be controlled without weakening overall security.
A VPN provides secure access by creating an encrypted link between an employee’s device and the company’s network. Through this connection, remote server access becomes possible without exposing internal systems directly to the open internet. Once connected, employees can access company resources as though they were physically present within the office.
This includes reaching an intranet site, internal dashboards, development environments, or document repositories that operate behind firewalls. The VPN acts as a controlled gateway.
Access control mechanisms determine who can enter and what they can see. Permissions are assigned based on role, ensuring that only authenticated users can reach specific network resources.
Authentication is critical. Businesses often require credentials, multi-factor verification, or digital certificates before granting network access. These layered checks prevent unauthorized entry and reduce the risk of compromised accounts spreading damage across the corporate network.
VPNs do not eliminate all security concerns, but they provide structure. They allow organizations to extend their internal infrastructure outward while maintaining corporate network protection.
In distributed work environments, this balance between accessibility and restriction becomes foundational. Without secure remote access, flexibility collapses. Without safeguards, exposure grows.
What a VPN Does NOT Protect You From?

A VPN strengthens your privacy and encrypts your traffic, but it does not solve every security problem. Understanding its limits prevents false confidence.
- Viruses: A VPN does not detect or remove viruses from your device. If malicious software is installed, encryption will not neutralize it. You still need antivirus tools and active security measures.
- Malware: Malware infections occur through compromised downloads, unsafe attachments, or vulnerable applications. A VPN does not scan files or block malicious code once it reaches your system.
- Phishing scams: Fraudulent emails and deceptive websites rely on social engineering, not network exposure alone. Even with encrypted traffic, you can still be tricked into revealing passwords or financial details.
- Free VPN risks: Free VPNs often monetize user data in indirect ways. Some may inject ads, track usage, or provide weak encryption. In extreme cases, free VPNs become the privacy risk they claim to solve.
- Logging policies: Not every VPN provider offers a strict zero log commitment. A weak vpn provider logging policy means your activity could still be recorded, stored, or shared under certain conditions.
A VPN improves privacy. It does not replace comprehensive cybersecurity practices.
How Do You Choose the Right VPN Provider?
Scroll through any app store or search result and you will see dozens of names competing for attention. Many VPN providers promise speed, privacy, anonymity, even freedom. The language is polished. The guarantees sound absolute. Choosing the right vpn provider requires more patience than impulse.
Start with fundamentals. A reliable vpn service should be transparent about how it operates, what encryption protocols it uses, and how it handles user data.
Strong vpn solutions are built on technical clarity, not marketing claims. Look beyond homepage slogans and examine documentation, independent audits, and public disclosures.
You also need to consider practical performance. The number and distribution of server locations directly influence speed and latency. A wider geographic spread often means better routing options and less congestion.
If you plan to use multiple devices, confirm that the service supports simultaneous connections without restrictive limitations.
These are core criteria to evaluate:
- Reputation and Track Record: A trustworthy vpn provider should have a documented history of reliability, independent reviews, and no unresolved security controversies.
- Zero-Log Policy: A clear logging policy should state that user activity is not recorded or stored. Ambiguous language around data retention is a warning sign.
- Encryption Standards: The vpn service should use modern encryption protocols such as AES 256-bit and well established tunneling methods to secure data traffic.
- Server Locations: A broad network of server locations improves performance, supports location flexibility, and reduces overcrowding on individual servers.
- Customer Support: Responsive support channels matter when technical issues arise. Look for live chat, detailed documentation, and timely assistance.
- Multi-device Support: The provider should allow secure connections across multiple devices, including laptops, mobile phones, and tablets under one account.
The decision should not be rushed. Privacy tools deserve scrutiny. A VPN can strengthen online privacy, but only when the provider itself operates with discipline and transparency.
Are VPNs Enough for Modern Network Security?
A VPN is powerful, but it is not a complete security architecture. It strengthens network security by encrypting traffic and controlling entry points, yet modern threats extend beyond simple interception. If you rely only on VPN technology, gaps can remain.
Traditional models assumed a clear perimeter. Once you entered the corporate network through a secure tunnel, you were trusted. That model worked when systems were centralized and employees stayed inside office walls.
Today, network infrastructure is distributed. Cloud services, third-party platforms, and remote endpoints expand the attack surface.
This is where the idea of Zero Trust gained traction. Instead of assuming trust after connection, Zero Trust frameworks verify continuously. Access control becomes granular. Each request to access sensitive data is evaluated individually. Permissions are limited to specific applications or systems rather than broad network entry.
A VPN provides secure access to the network. Zero Trust extends that concept by questioning every action within it. The difference is subtle but meaningful. Secure entry does not guarantee secure behavior afterward.
VPNs remain essential for encrypting connections and protecting data in transit. They help secure sensitive data as it moves across networks. However, they do not monitor device posture, detect compromised credentials automatically, or segment internal systems by default.
In short, VPN technology is foundational but not sufficient alone. Modern security strategies layer encryption, access control, monitoring, and verification together. The tunnel is necessary. It is not the entire structure.
Final Thoughts
By now, the mechanics are clearer. A VPN works by encrypting your internet traffic, routing it through a remote server, and masking your IP address before data reaches its destination.
That process creates a secure connection across networks that were never designed with privacy as a priority. It protects data in transit. It reduces visibility.
So should you use a VPN in 2026?
If you rely on public Wi Fi networks, handle sensitive information, or require remote access to company systems, the answer is straightforward. A VPN adds a practical layer of protection. It strengthens online privacy and limits exposure to tracking from internet service providers and third parties.
At the same time, clarity matters. A VPN does not replace antivirus software. It does not eliminate phishing risks. It does not guarantee anonymity. There are security trade-offs, including slight performance overhead and the need to trust your chosen provider.
The decision should not be driven by fear or marketing slogans. It should be driven by context. Assess how you use the internet, what data you transmit, and how much control you want over your digital footprint.
Frequently Asked Questions (FAQs)
1. How does a VPN actually work?
A VPN works by encrypting your internet traffic on your device and routing it through a remote server operated by a VPN provider. That server masks your IP address, creating a secure connection that protects data from interception.
2. What is the difference between a VPN and a proxy?
A VPN encrypts all network traffic from your device and secures the entire internet connection. A proxy usually redirects traffic for a single app or browser session and often does not provide strong encryption or full network protection.
3. Can a VPN completely hide your online activity?
A VPN masks your IP address and encrypts browsing data, reducing visibility to internet service providers and network observers. However, websites can still track behavior through cookies, accounts, and device fingerprinting, so anonymity is not absolute.
4. Are free VPNs safe to use?
Some free VPNs offer basic encryption but impose data limits or speed restrictions. Others may log user activity or sell usage data. Always review the provider’s logging policy and security standards before trusting a free service.
5. What is the most secure VPN protocol?
OpenVPN is widely regarded as highly secure due to its strong encryption and open-source transparency. IKEv2 and IPSec also provide robust protection. Security depends on proper configuration and the quality of the VPN provider’s implementation.
6. Does a VPN slow down internet speed?
A VPN can reduce speed slightly because encryption and server routing add processing time. However, it may help avoid bandwidth throttling by hiding traffic type from your internet service provider, which can offset performance loss in some cases.
7. Can businesses rely only on VPN for security?
A VPN secures remote access and encrypts data in transit, but it does not provide complete network security. Businesses often combine VPNs with access control policies, monitoring tools, and Zero Trust frameworks for broader protection.