The rules of cybersecurity have changed. As remote work, multi-cloud adoption, and mobile access become the norm, traditional network security models are struggling to keep up.
The old castle and moat approach, where everything inside the network perimeter was trusted, no longer holds. Attackers don’t need to break through walls anymore; they log in with stolen credentials or exploit weak access controls.
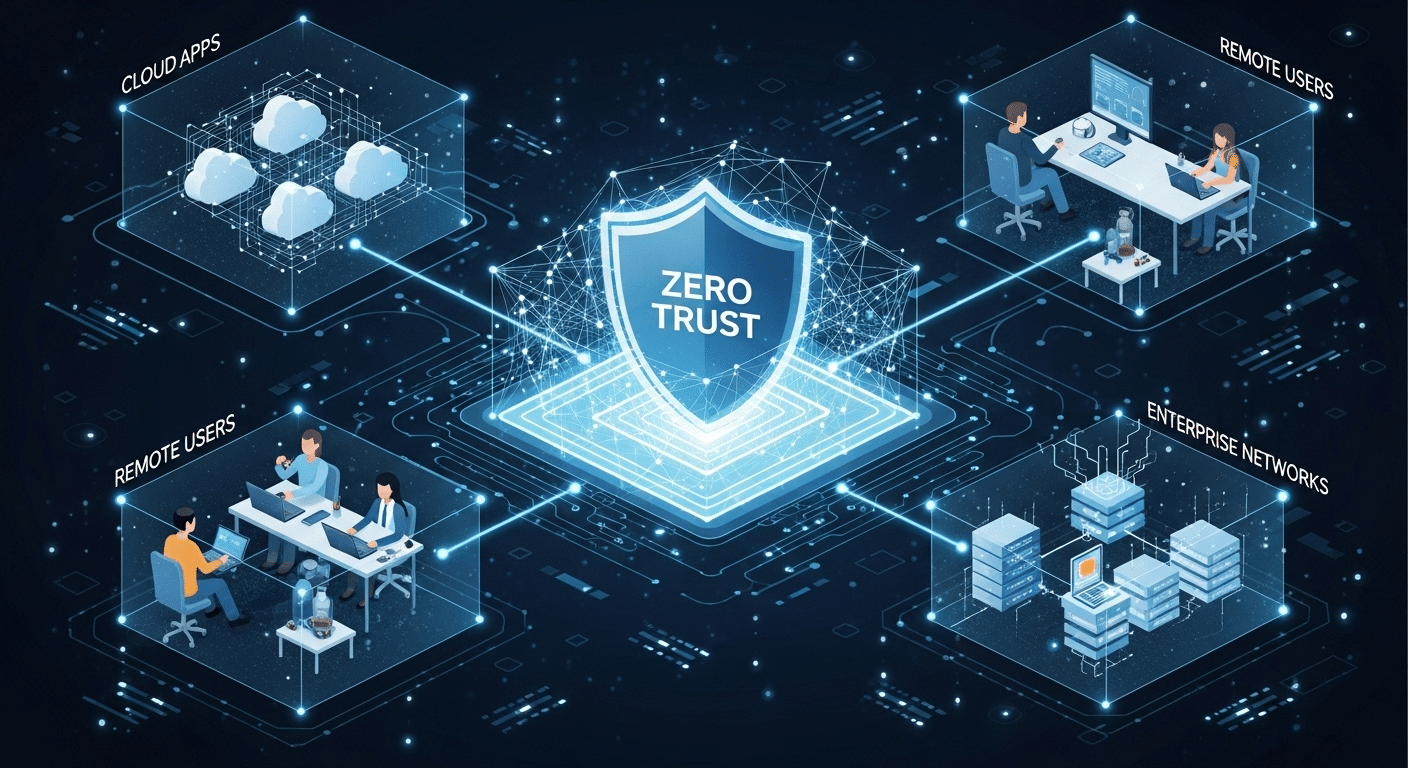
This growing complexity has made Zero Trust security the new gold standard. Its philosophy is simple but powerful: never trust, always verify.
Every user, device, and connection must continuously prove it deserves access, whether inside or outside the corporate network.
In this guide, you’ll explore what Zero Trust is, how it works, its core principles, the benefits it delivers, and practical steps to help you adopt it effectively.
What Exactly Is Zero Trust?
At its core, Zero Trust is a modern security framework built on a straightforward idea: implicit trust is a vulnerability. In traditional systems, once you’re inside the network, you’re trusted by default.
Zero Trust changes that logic entirely. Every user, device, and application must continually prove its legitimacy, no matter where it’s located or what it’s accessing.
The Zero Trust security model enforces strict access controls and continuous verification. Instead of granting blanket access, it allows users to connect only to the specific resources or applications they need.
This ensures that even if credentials are stolen or a system is compromised, the attacker’s movement across the organization’s network is limited.
In a Zero Trust architecture, every action is governed by policies tied to user identity, device health, and contextual risk. All activity, whether a login or a file download—is monitored, analyzed, and verified in real time.
You can think of it as a trust security model where access control happens everywhere, not just at the edge of the network. By removing assumptions and replacing them with verification, Zero Trust gives you a stronger, more adaptable defense against modern cyber threats.
How Does Traditional Security Differ from the Zero Trust Model?
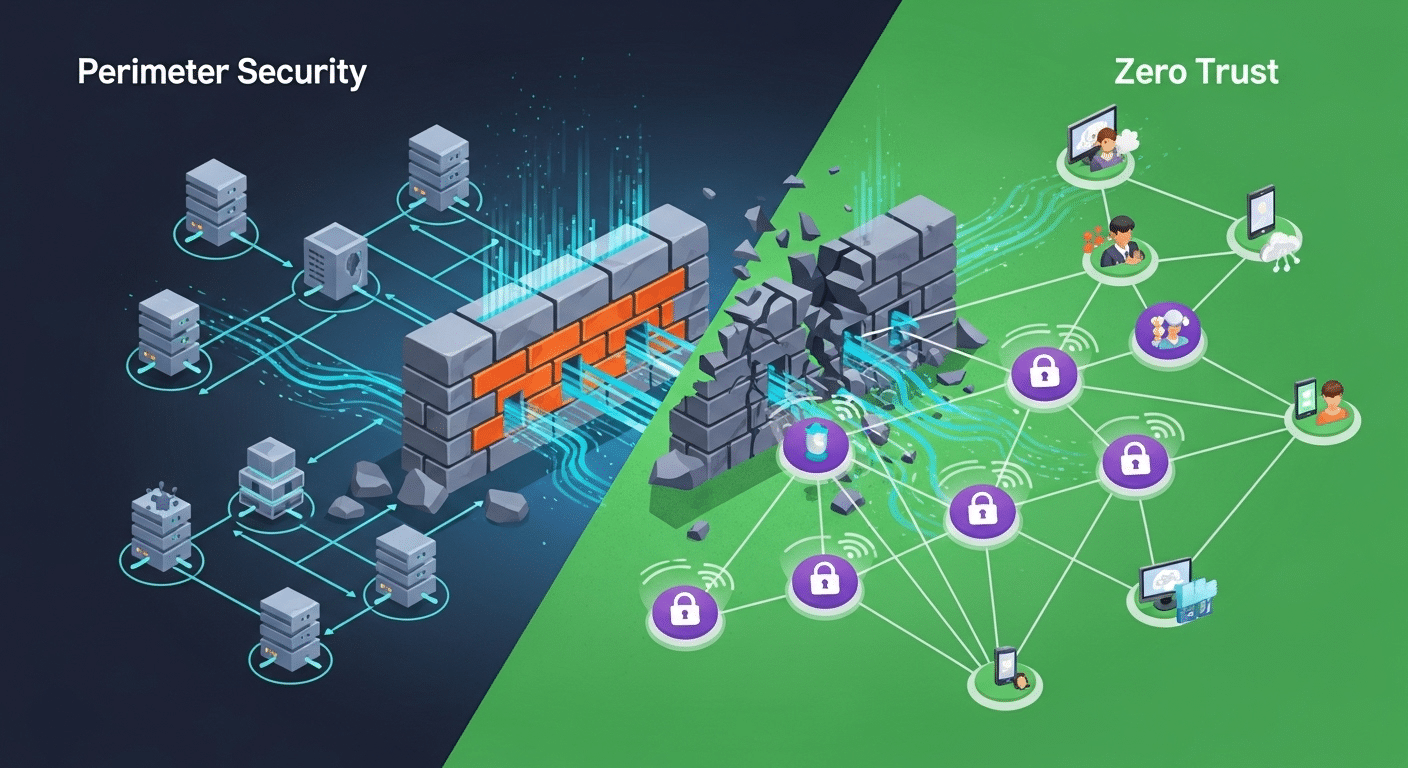
Traditional network security relied on a simple boundary: protect what’s inside the network perimeter and keep outsiders out. This “castle and moat” model trusted internal users by default.
But once attackers breached that outer wall, often through phishing or stolen credentials, they could move freely, accessing sensitive data without resistance.
The Zero Trust model removes that flaw by eliminating implicit trust. It operates on the rule of never trust, always verify. Every access request is checked against factors like user identity, device compliance, location, and behavior. If something looks suspicious, access is denied or restricted automatically.
Instead of providing entry to the entire network, Zero Trust limits permissions to specific resources through least privilege access and microsegmentation. These methods ensure that even if one segment is compromised, the rest remains protected.
In essence, Zero Trust transforms security from a single barrier to a network of continuously verified checkpoints—stronger, smarter, and more aligned with today’s digital landscape.
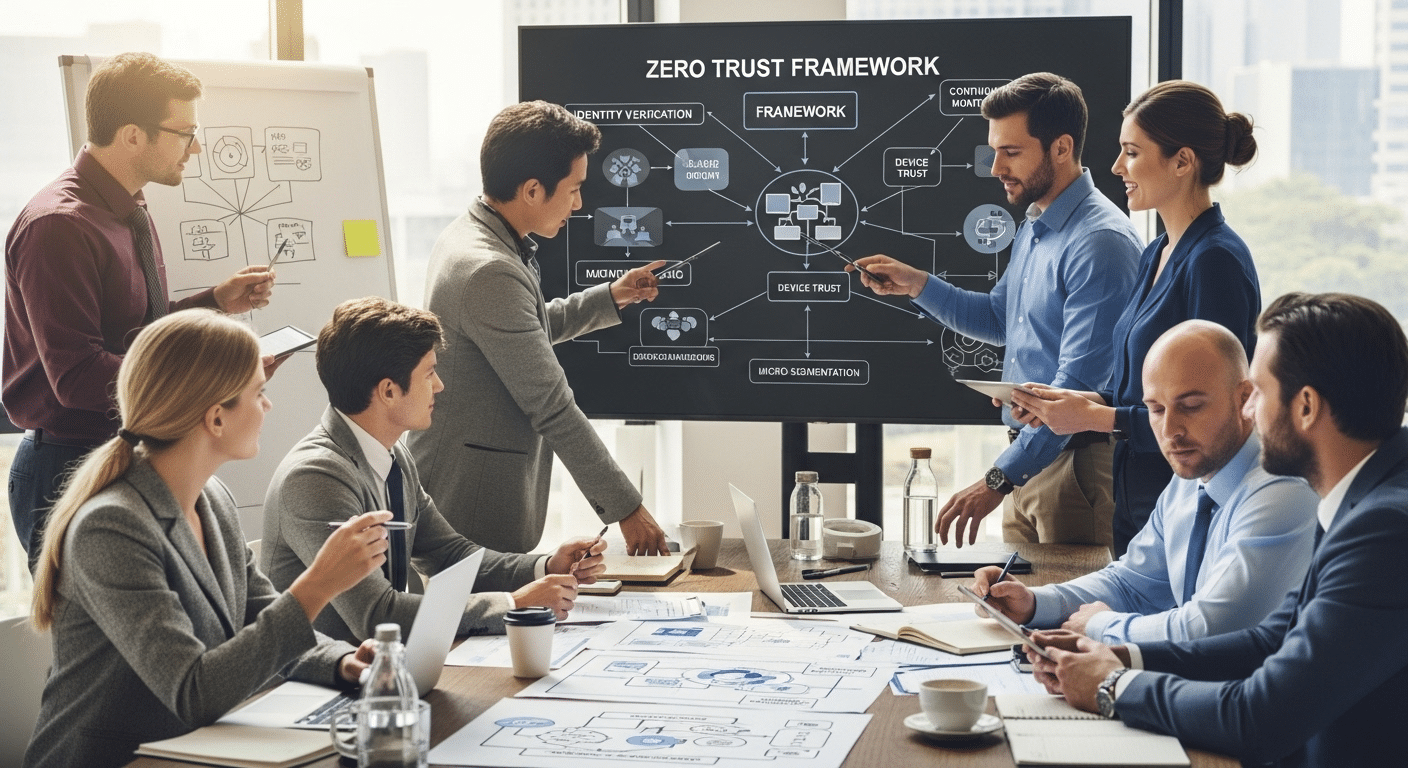
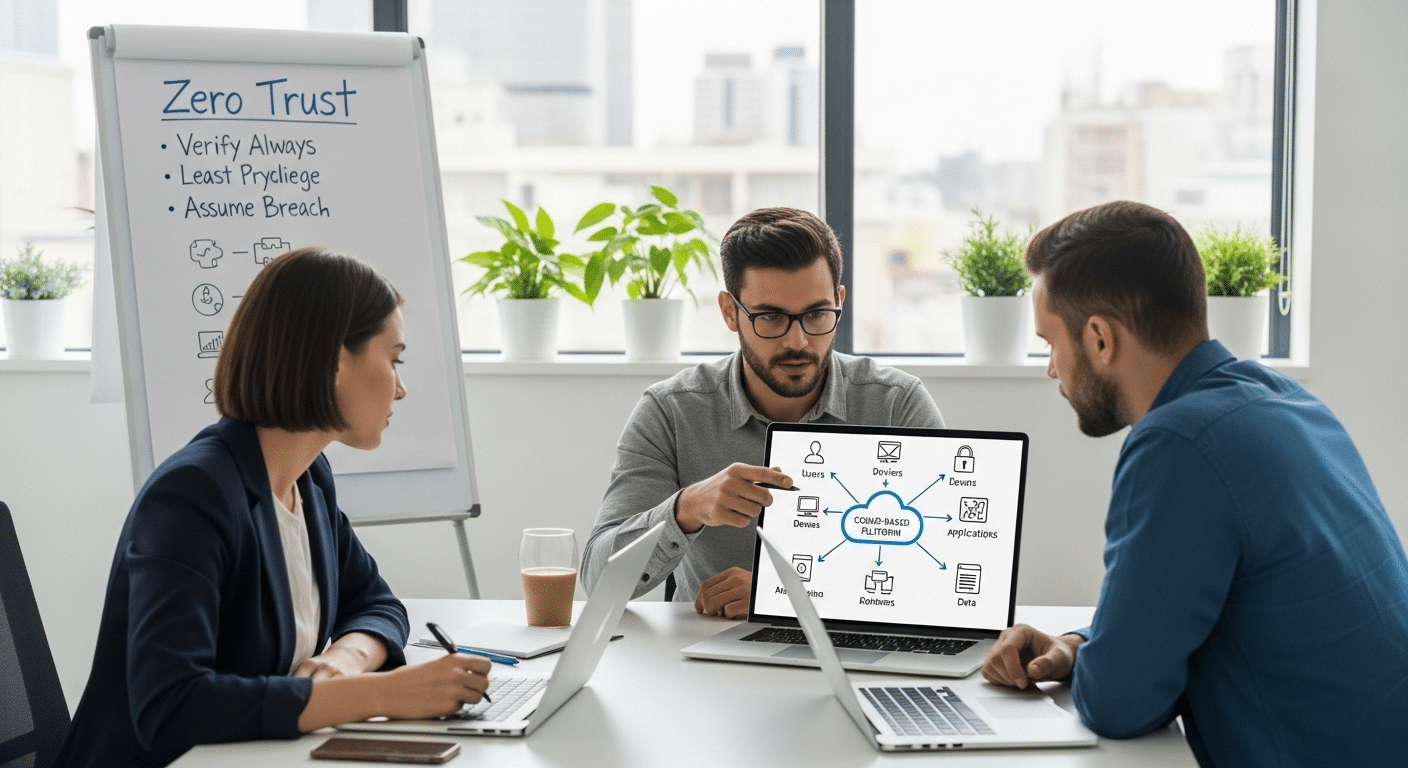
What Are the Core Principles of Zero Trust?
The Zero Trust security model isn’t a single product or tool, it’s a mindset shaped around five core principles that redefine how you protect your organization’s data, devices, and users. These Zero Trust principles form the foundation of a strong security posture and help align teams with frameworks like NIST’s Zero Trust Architecture.
Least Privilege Access
Every user is given access only to the resources necessary for their role, nothing more. This limits exposure and minimizes potential damage from compromised accounts. By enforcing least privilege access, your organization drastically reduces the chance of unauthorized activity.
Continuous Verification
Zero Trust replaces one-time logins with continuous verification. Every session, device, and user identity is reassessed in real time. Even if a device or credential was verified earlier, the system constantly monitors network traffic for anomalies.
Microsegmentation
Instead of treating the network infrastructure as one open space, it’s divided into secure segments. If one area is breached, attackers can’t move laterally across the network, each zone is isolated and protected by its own access controls.
Multi-Factor Authentication (MFA)
Passwords alone are no longer enough. MFA adds extra layers, like biometric or code-based verification, to confirm user identity, preventing unauthorized access even if credentials are stolen.
Assume Breach
Zero Trust works on the assumption that a breach will happen. This proactive stance shifts the focus from mere prevention to rapid detection and response, strengthening overall resilience.
Together, these trust principles create a security framework that continuously adapts to evolving threats. Whether you’re managing cloud environments, remote users, or on-prem systems, Zero Trust ensures security is verified, not assumed.
How Does Zero Trust Architecture Actually Work?
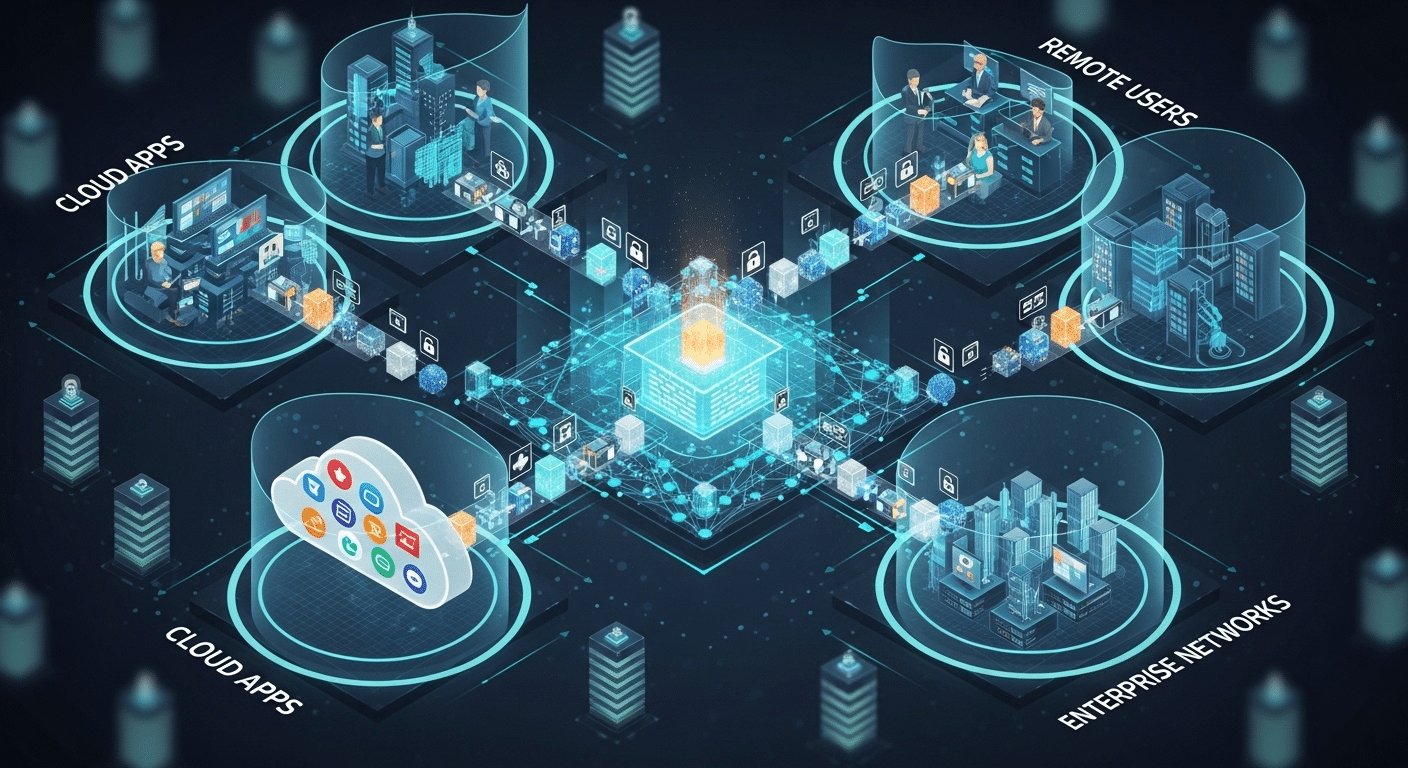
A Zero Trust Architecture (ZTA) transforms the way access is managed across your organization. Instead of defending a single network perimeter, it enforces security controls everywhere, on users, devices, and applications.
At the heart of ZTA is Zero Trust Network Access (ZTNA), which replaces traditional VPNs. Rather than granting full access to the corporate network, ZTNA limits access to specific resources or applications. Each request is evaluated based on user identity, device health, and contextual risk, ensuring only authorized users and compliant devices gain entry.
ZTA operates through policy enforcement points that verify trust continuously. It monitors network behavior, runs risk assessments, and uses threat intelligence to detect abnormal patterns.
These layers help maintain control even as environments become more distributed and dynamic.
Both public and private sectors are embracing this model. Federal agencies and the Cybersecurity and Infrastructure Security Agency (CISA) have made ZTA part of national standards, signaling its importance beyond enterprise networks.
Briefly, Zero Trust Architecture enables secure access in a world without borders—ensuring that every action, connection, and device is continuously verified before trust is granted.
Why Is Zero Trust Adoption Growing So Quickly?
The cybersecurity landscape has shifted dramatically. The rise of remote access, personal devices (BYOD), and multi-cloud environments has blurred the traditional network perimeter.
Attackers now target credentials, third-party vendors, and even software updates, making traditional models ineffective.
Zero Trust offers a modern answer. By enforcing least privilege access and continuous monitoring, it reduces the attack surface and prevents threats from spreading inside your network.
This proactive approach strengthens your security posture, even when users and data are dispersed globally.
Governments and enterprises alike are taking notice. The Federal Zero Trust Strategy requires agencies to adopt Zero Trust architectures, setting an example for the private sector. Meanwhile, security teams are finding it a scalable way to manage access in complex ecosystems.
As organizations face increasing insider threats, supply chain attacks, and compliance demands, Zero Trust provides a consistent security framework that adapts to any environment—cloud, on-prem, or hybrid. It’s not just a trend; it’s quickly becoming the foundation of cybersecurity itself.
What Are the Core Benefits of Zero Trust for Organizations?
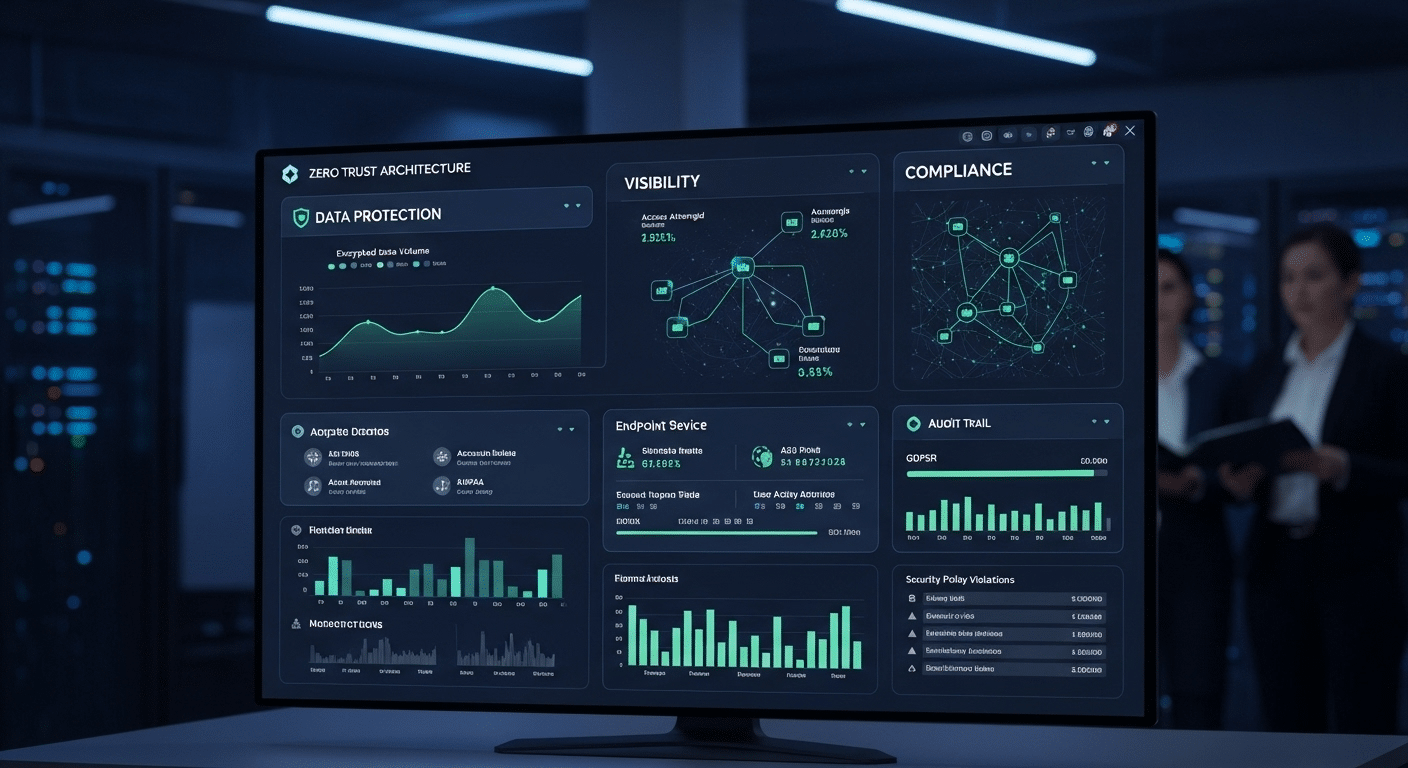
Implementing a Zero Trust security model offers wide-ranging benefits that go beyond just blocking threats—it helps you build a smarter, more resilient security posture tailored to modern risks.
- Protects Sensitive Data
With a combination of network segmentation, encryption, and strict access control policies, Zero Trust reduces unauthorized access to intellectual property, customer data, and regulated information. - Reduces Insider Threats
By enforcing least privilege access, employees and contractors only access what they need to perform their roles. This lowers the risk of intentional or accidental misuse of data. - Improves Visibility and Control
Continuous monitoring provides real-time insights into network traffic, access requests, and user behavior. This level of transparency strengthens response times and overall security posture. - Boosts Compliance Readiness
Meeting data regulations like HIPAA, GDPR, FERPA, or CMMC becomes more manageable when systems automatically enforce Zero Trust policies and log activity. - Adapts to Modern IT Environments
Whether you’re operating in cloud environments, on-premises systems, or hybrid setups, Zero Trust applies uniformly across the entire network. - Business Resilience
By limiting access scope and using privilege access controls, breaches can be isolated quickly, minimizing operational impact.
Zero Trust doesn’t just stop cyberattacks—it enhances how your organization operates, adapts, and recovers in the face of evolving threats.
How Can Zero Trust Help Mitigate Insider Threats and Supply Chain Risks?
Many of today’s breaches don’t come from outside, they originate from within. Whether intentional or accidental, insider threats are among the hardest to detect. Zero Trust helps reduce these risks with layered security and strict verification at every step.
For starters, least privilege access ensures that no user can see or interact with more than their role requires. Combined with continuous verification and behavioral analytics, unusual activity is spotted early, often before damage is done.
When it comes to supply chain risks, Zero Trust Network Access (ZTNA) plays a critical role. Instead of granting third-party vendors broad access, ZTNA isolates their access to specific systems or applications.
This protects the trust network from lateral movement if a partner system is compromised.
Other tools, like threat intelligence and real-time monitoring, strengthen your ability to detect and respond to anomalies, whether they stem from a careless employee or a compromised vendor.
By treating every connection as untrusted until proven otherwise, Zero Trust policies limit both human error and malicious intent. It’s a practical and scalable way to address two of today’s biggest cybersecurity concerns.
What Steps Are Involved in Implementing a Zero Trust Strategy?
Rolling out a Zero Trust strategy doesn’t have to be overwhelming. By breaking it into clear, manageable steps, your team can adopt the model gradually, without major disruptions.
- Assess your environment
Start by identifying users, devices, and network resources. Map who needs access to what, and from where. - Define access policies
Create rules based on identity, device security, and contextual factors. Incorporate risk-based authentication to adapt dynamically. - Apply IAM and MFA
Use Identity and Access Management (IAM) tools to enforce roles and permissions. Add Multi-Factor Authentication (MFA) for extra protection at login points. - Segment the network
Break your network infrastructure into smaller zones. This prevents unauthorized lateral movement and limits exposure if a breach occurs. - Implement ZTNA and monitoring
Deploy Zero Trust Network Access tools and set up continuous monitoring to track access requests and network behavior. - Review and refine
Use security analytics and user behavior insights to adjust policies and improve trust architecture over time.
By starting small, targeting high-risk areas first—you can scale Zero Trust across your organization with minimal friction. It’s a long-term investment in security, but one that starts with a few strategic steps..
What Are the Common Challenges of Zero Trust Implementation?
Implementing Zero Trust isn’t always smooth. Legacy systems often lack compatibility with modern Zero Trust frameworks, making integration tricky. Existing infrastructure may need upgrades, which can stretch timelines and budgets.
Then there’s internal resistance. Security teams and employees used to perimeter-based models may push back, especially if access controls are rolled out too aggressively. Poor implementation can lead to user frustration and workflow slowdowns.
Adding too many disconnected security tools can also cause fatigue and confusion, hurting adoption instead of helping it. And for small and mid-sized businesses, limited resources and budget can slow progress.
The solution? Start with high-risk areas or sensitive data environments. Apply Zero Trust policies gradually, testing and refining along the way. This phased approach reduces disruption and helps build long-term support.
Is Zero Trust Suitable for Small and Mid-Sized Organizations?
Absolutely. Zero Trust isn’t reserved for federal agencies or tech giants. In fact, SMBs face many of the same threats—just with fewer layers of protection.
The good news is that Zero Trust principles scale well. Tools like ZTNA, MFA, and IAM can be deployed in lightweight, budget-friendly ways. Solutions like Apporto offer built-in Zero Trust access without requiring heavy infrastructure or extensive IT teams.
Smaller networks and simpler user structures also mean faster rollouts. For SMBs, Zero Trust isn’t just possible, it’s often more achievable than it is for large, complex enterprises.
What Tools and Technologies Support a Zero Trust Environment?
A successful Zero Trust environment relies on multiple technologies working together. Main components include:
- Zero Trust Network Access (ZTNA): Controls who can access what, based on identity, risk, and context.
- Identity and Access Management (IAM): Validates user identity and enforces access management rules.
- Multi-Factor Authentication (MFA): Adds another layer of login security.
- Endpoint Detection and Response (EDR): Monitors device behavior for suspicious activity.
- Cloud Access Security Broker (CASB): Manages data and app use across cloud environments.
- Threat Intelligence: Flags high-risk behaviors and indicators of compromise.
When integrated, these tools form the backbone of a Zero Trust architecture, enhancing visibility and minimizing risk across your entire IT infrastructure.
Final Thoughts
Zero Trust isn’t a quick fix, it’s a long-term security strategy that reshapes how your organization thinks about access. Instead of assuming trust, it ensures that every access request is verified and earned through identity, context, and risk.
Start small. Apply Zero Trust where the risks are highest, and scale gradually as your teams adapt.
Platforms like Apporto make it easier by delivering a browser-based Zero Trust environment—perfect for education, remote teams, and SMBs seeking smarter, scalable protection.
In the future, trust won’t be assumed. It will be designed.
Frequently Asked Questions (FAQs)
1. What does “never trust, always verify” mean?
It means no user or device is trusted by default, every login and access request is continuously verified.
2. How is Zero Trust different from traditional network security?
Traditional models secure the network perimeter. Zero Trust assumes risk everywhere and validates every connection, inside or out.
3. Can Zero Trust protect cloud and remote environments?
Yes. It applies consistent security policies across cloud, hybrid, and remote access systems.
4. What is ZTNA in simple terms?
Zero Trust Network Access (ZTNA) grants users secure, limited access to specific apps, not the whole network.
Is Zero Trust expensive or hard to implement?
Not with the right tools. Solutions like Apporto make Zero Trust affordable and scalable, especially for SMBs and education.